Category Archives: technology
WIPO
Despite the dominance of companies in AI, universities and public research organizations play a leading role in inventions in selected AI fields such as distributed AI, some machine learning techniques and neuroscience/neurorobotics.
Chinese organizations make up 17 of the top 20 academic players in AI patenting as well as 10 of the top 20 in AI-related scientific publications. Chinese organizations are particularly strong in the emerging technique of deep learning. The leading public research organization applicant is the Chinese Academy of Sciences (CAS), with over 2,500 patent families and over 20,000 scientific papers published on AI. Moreover, CAS has the largest deep learning portfolio (235 patent families). Chinese organizations are consolidating their lead, with patent filings having grown on average by more than 20 percent per year from 2013 to 2016, matching or beating the growth rates of organizations from most other countries.
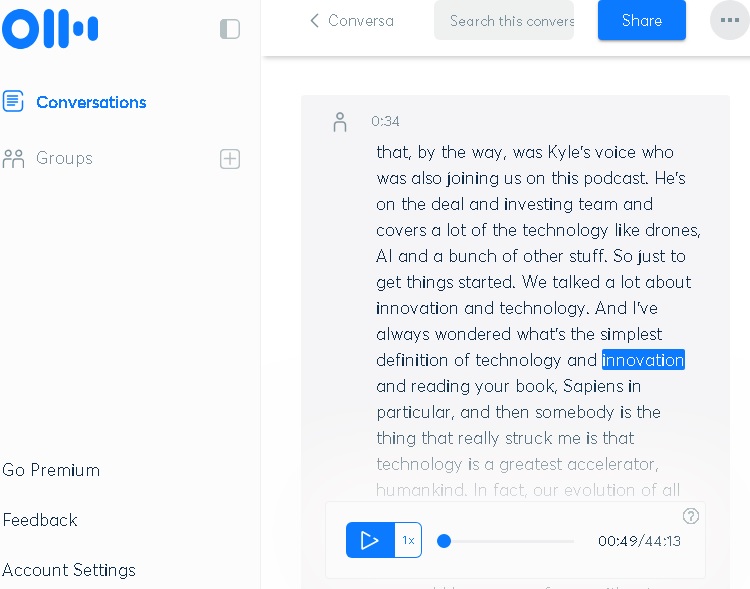
Otter
Agility Robotics
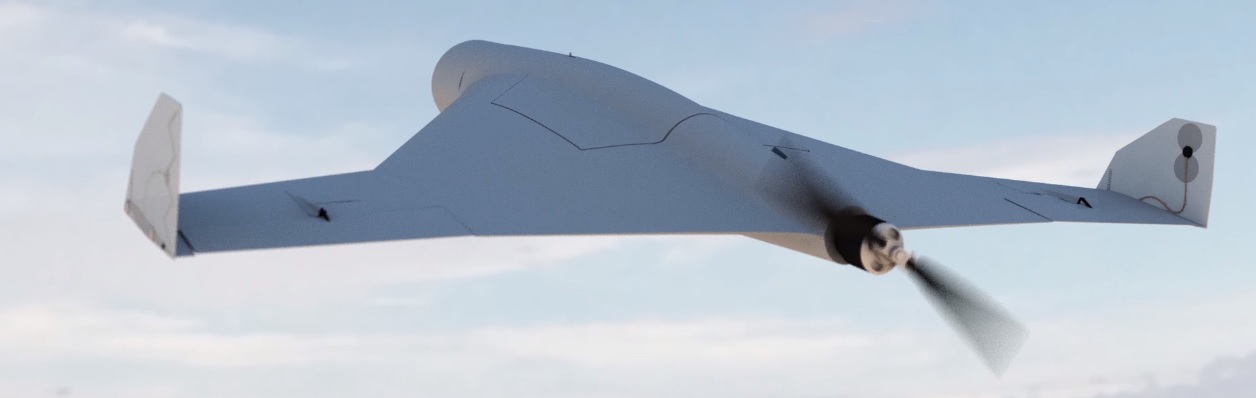
Сергей Чемезов

Этот комплекс – это шаг к абсолютно новому ведению боевых действий. Мы уверенно держимся в первых рядах среди стран-производителей такого рода вооружений. Высокоточный беспилотный снаряд летит до 30 минут со скоростью 130 км в час. Заряд на данном комплексе доставляется к цели вне зависимости от ее скрытности и рельефа местности – как малых, так и на больших высотах. Это очень точное и максимально эффективное оружие, с которым очень трудно бороться с помощью традиционных средств ПВО.
伊藤恵理
 最近では、TEDやTEDxといったトークショーで、科学技術者のアイデアをスタイリッシュに世界に発信できる機会も増えました。また、STEAMが誕生したりして、科学を伝えるコミュニケーションの大きな進歩を嫡しく思っています。
最近では、TEDやTEDxといったトークショーで、科学技術者のアイデアをスタイリッシュに世界に発信できる機会も増えました。また、STEAMが誕生したりして、科学を伝えるコミュニケーションの大きな進歩を嫡しく思っています。
その反面、科学技術や社会実装の仕組みが理解されないまま、一部でイメージばかりが先行する状況に不安を感じるようにもなりました。AI、ロボット、自動運転車、ドローン、シンギュラリティなどについて、多くの専門家が、一般社会の捉え方とのギャップに違和感を覚えています。
科学技術の発展に伴って、豊かな未来を築くためには、文系・理系の壁を超え、時代に合った正しい科学リテラシーを身につける必要があります。
Devin Coldewey
 The planned Robot Science Museum in Seoul will have a humdinger of a first exhibition: its own robotic construction. It’s very much a publicity stunt, though a fun one — but who knows? Perhaps robots putting buildings together won’t be so uncommon in the next few years, in which case Korea will just be an early adopter.
The planned Robot Science Museum in Seoul will have a humdinger of a first exhibition: its own robotic construction. It’s very much a publicity stunt, though a fun one — but who knows? Perhaps robots putting buildings together won’t be so uncommon in the next few years, in which case Korea will just be an early adopter.
Drago Anguelov
Минобороны России
串間充崇
イエバエからは植物用の肥料と動物用の飼料を製造することができます。イエバエの幼虫の排泄物をペレット化したものが肥料に、幼虫を乾燥させたものが動物性タンパク質飼料になります。この肥料や飼料の効果は、わかりやすくいえば栄養が豊富なこと。例えばイエバエでつくった餌を食べた魚は、通常の餌で育てるより約4割も大きく育ちます。つまり、餌の量を半分くらいに減らしても、いままでと同じ大きさの食用魚を提供できるわけです。また、最高級飼料よりも魚たちが好んで食べてくれます。肥料には、農作物の収穫量を増やすほか、病原菌を抑制してくれる働きがあります。
さらに注目すべきは、「食料残渣(食品製造や外食産業でうまれる余剰物)」と「畜糞(家畜の排泄物)」を処理できることです。いまは食料残渣の多くが焼却処理されるほか、畜糞は日本だけでも年間8,000万トンが排出されており、現在は広大な土地で2〜3カ月かけて微生物によって分解されています。しかもこの処理でメタンガスなどの有害な発酵ガスが発生します。ところがイエバエの幼虫は、これらを食べてくれます。彼らは畜糞の窒素分を吸収し、消化酵素がかかった土は肥料に変換し、そのあと土から出た幼虫は乾燥して飼料にします。つまり、これまで処理にコストがかかっていた廃棄物が原料になるため、お金をもらいながらイエバエを育てることができる。無から有をつくるのではなく、マイナスだったものからプラスを生み出すことができるんです。
これにより、化学物質に頼らなくても、これまで不要とされてきた畜糞で動物や植物を育てることができる。イエバエの技術をうまく利用できれば、完全に自然な食物連鎖での食糧生産も実現するはずです。
INCOMPLETE++
Otter.ai
パソコンハードウェア初心者の館
- マウスコンピューター / G-Tune ★
デザインと高性能を両立、価格も安めで、ここ10年で急成長したメーカー。 - ドスパラ (Dospara) ◎
高性能なデスクトップを安く手に入れたいなら定番の1つ。 - 日本HP (ヒューレット・パッカード) ◎
デザイン重視の個人向けのモデルが中心。ノート 、スリムデスクトップが得意。 - DELL (デル) ○
安さで勝負。デザインや追加機能よりもコストパフォーマンス優先。 - Microsoft(マイクロソフト) ○
Windows の会社。2012 年から 2in1 モデルを販売し、急速にシェアを拡大。 - Lenovo (レノボ) △
中国のメーカーで安い。ビジネス用が中心で、堅牢さと安定性を重視。 - Apple(アップル、Mac) *
独自規格。ソフトや周辺機器は専用品が必要。デザイン等に優れるが高価。
Carnegie Mellon University
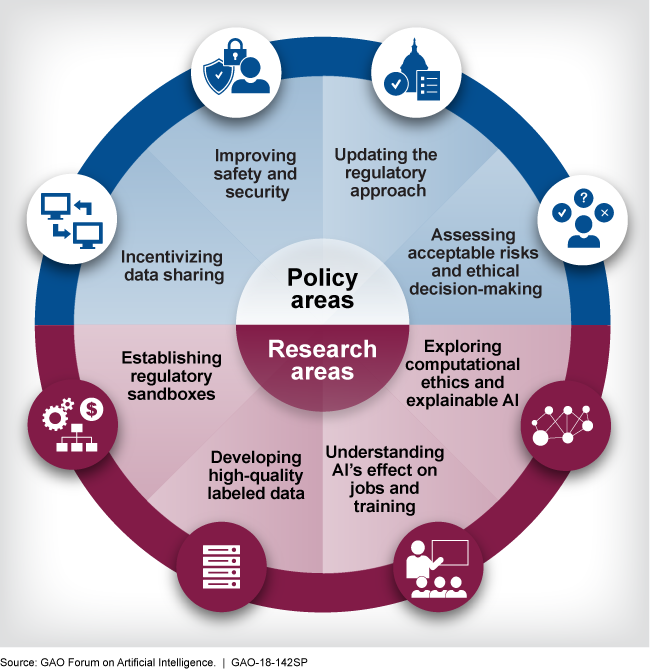
GAO Forum on Artificial Intelligence (AI)
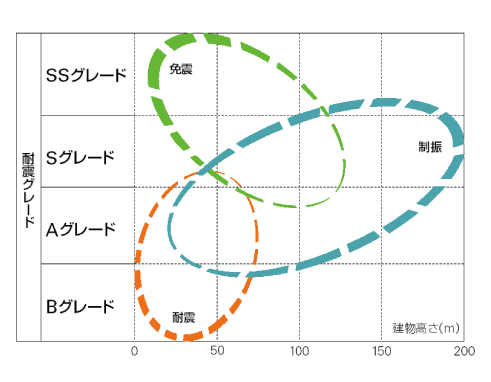
日建設計
RYNO Motors
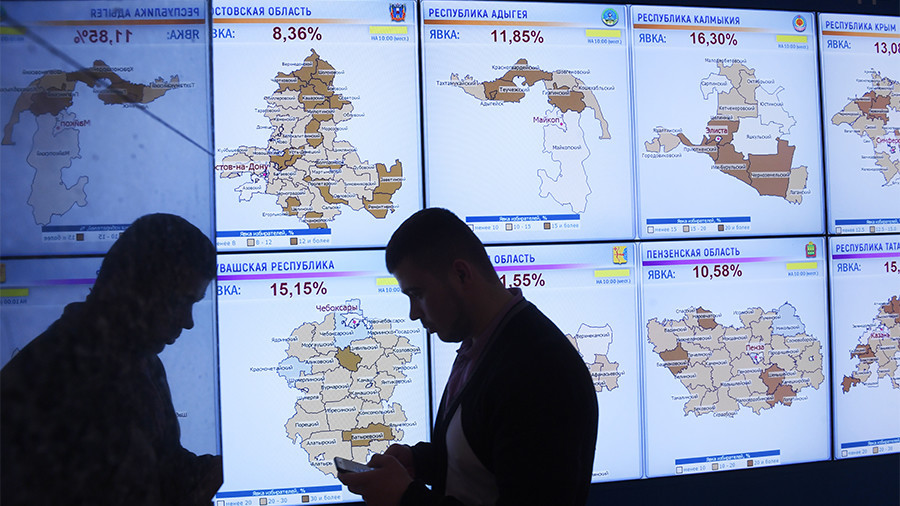
РБК
Wikipédia
 Un compteur communicant est un compteur disposant de technologies dites AMR (Automated Meter Reading) qui mesure de manière détaillée et précise, et éventuellement en temps réel, une consommation d’électricité, d’eau ou de gaz. La transmission des données s’effectue par ondes radio ou par courants porteurs en ligne (CPL) au gestionnaire du réseau de distribution chargé du comptage.
Un compteur communicant est un compteur disposant de technologies dites AMR (Automated Meter Reading) qui mesure de manière détaillée et précise, et éventuellement en temps réel, une consommation d’électricité, d’eau ou de gaz. La transmission des données s’effectue par ondes radio ou par courants porteurs en ligne (CPL) au gestionnaire du réseau de distribution chargé du comptage.
Les compteurs communicants servent à produire des factures sur la consommation réelle, à repérer des gaspillages, des pertes en ligne ou les postes qui coûtent le plus au client. Ils peuvent éventuellement l’informer de microcoupures ou de pertes des réseaux électriques.
Si le compteur est en outre « programmable à distance » et équipé d’un appareil de coupure à distance, il est dit « AMM » (Advanced Meter Management). Ces fonctions sont à la base de l’évolution des réseaux (d’électricité, d’eau ou de gaz) vers les « réseaux intelligents ».
Kristin Burnham
Imagine sitting in your car in a drive-through, just after ordering a cup of coffee. As you wait for the barista to make your drink, a stranger opens your passenger door, reaches for the gas pedal, and floors it. Your car is burning gas quickly and could be sustaining damage to its engine.
Now imagine that the car is your computer, and the stranger is code running in your Web browser.
Congratulations, you’re a victim of cryptojacking, a relatively new method of mining cryptocurrency that involves harvesting an external device’s processing and electrical power to perform transaction-validating cryptographic calculations. As cryptojackers leech power from and compromise site visitors’ hardware, they line their pockets with portions of the bitcoin, litecoin, monero, ethereum, and other cryptocurrencies they mine.
Kathleen Fisher
Securing code for cars is not impossible.
There’s a ton we could do to make cars more secure.
The tech exists; it’s more a question of the will.
Boeing
 The Boeing EA-18G Growler is an American carrier-based electronic warfare aircraft. The Growler’s electronic warfare capability is primarily provided by Northrop Grumman.
The Boeing EA-18G Growler is an American carrier-based electronic warfare aircraft. The Growler’s electronic warfare capability is primarily provided by Northrop Grumman.
The added electronics include AN/ALQ-218 wideband receivers on the wingtips and ALQ-99 high and low-band tactical jamming pods. The ALQ-218 combined with the ALQ-99 form a full spectrum electronic warfare suite that is able to provide detection and jamming against all known surface-to-air threats.
FUJITSU
モバイルネットワーク
- 1G:第1世代(アナログ無線、アナログ携帯電話)
- 2G:第2世代(データ通信、デジタル携帯電話)
- 3G:第3世代(脱地域限定、世界標準)
- 4G:第4世代(高速化、スマートフォン)
- 5G:第5世代(すべての端末・アプリケーション)
John Leyden, Chris Williams
A fundamental design flaw in Intel’s processor chips has forced a significant redesign of the Linux and Windows kernels to defang the chip-level security bug.
Programmers are scrambling to overhaul the open-source Linux kernel’s virtual memory system. Meanwhile, Microsoft is expected to publicly introduce the necessary changes to its Windows operating system in an upcoming Patch Tuesday: these changes were seeded to beta testers running fast-ring Windows Insider builds in November and December.
Crucially, these updates to both Linux and Windows will incur a performance hit on Intel products. The effects are still being benchmarked, however we’re looking at a ballpark figure of five to 30 per cent slow down, depending on the task and the processor model. More recent Intel chips have features – such as PCID – to reduce the performance hit. Your mileage may vary.
Morgane Tual
L’être humain est-il menacé par la technologie ?
La machine risque-t-elle de le dominer ?
Fantasmes ou réalité ?
L’emploi menacé ?
Des données biaisées ?
Vers un « piratage » de l’esprit humain ?
Interdire les armes autonomes ?
Tous surveillés ?
Comment protéger les données personnelles ?
Expliquer l’inexplicable ?
Responsables mais pas coupables ?
QNNcloud
Problems involving combinatorial and continuous optimization are ubiquitous in our modern life. Classic examples include lead compound optimization in the development of medicine, frequency band and/or transmission power optimization in wireless communications, sparse coding for compressed sensing, Boltzmann sampling in machine learning, portfolio optimization in Fin Tech, and many others. Most of those problems belong to the non-deterministic polynomial (NP), NP-complete, and NP-hard classes in complexity theory and require exponential resources as the problem size increases. The QNN exploits quantum parallel searching at below OPO threshold, collective symmetry breaking at OPO threshold, and exponential probability amplification of the solution state at above OPO threshold to address this limitation.
Boston Dynamics
Virginia Tech, Ford
Greg Nichols
AI is spreading to the enterprise at a phenomenal rate.
According to a global survey of 260 large organizations, a data and analytics company, 80 percent of enterprises are investing in AI and one in three “believe their company will need to invest more over the next 36 months to keep pace with competitors.”
Let’s get this out of the way: What is AI?
Like “Big Data,” it’s a buzz phrase and technology category that’s at once alluring and elusive. In general, enterprise AI includes things like machine and deep learning, voice recognition and response, Robotic Process Automation (RPA), automated communications and reporting, predictive analytics, and recommendation engines.
If you’re a purist, you’ll recognize that a more accurate description for most of these technologies would be software automation. But that’s less fun to throw around at parties.
Big Data is distinct from AI, but the Big Data revolution that started a few years back has enabled many of the technologies we’re calling AI.
If you’re positioned to drive adoption and deployment of any of these technologies, which many IT professionals are, you’re sitting on a huge opportunity, and potentially a leap into the C-suite.
Andrew Ng
Acme Portable Machines
The DuraPAC Pro is a powerful and robust portable computer suitable for tough environments and mobile applications. The aluminum and steel construction allows for it to be both lightweight and rugged. The steel design maintains the ruggedness and integrity of the model while at the same time, the aluminum allows it to be lightweight.
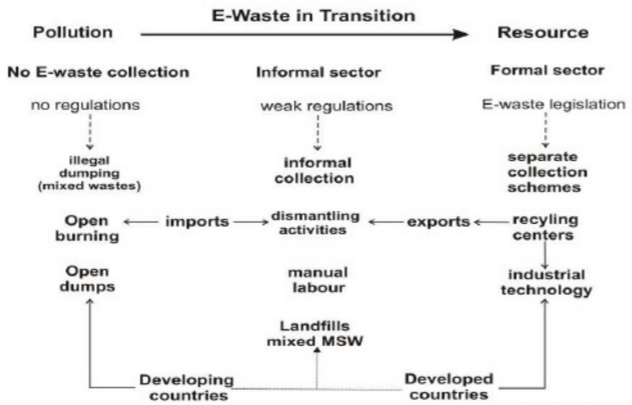
Florin-Constatin Mihai, Maria-Grazia Gnoni
Martin Untersinger
WordPress
503 Service Unavailable
Service Temporarily Unavailable
The server is temporarily unable to service your request due to maintenance downtime or capacity problems. Please try again later.
Additionally, a 404 Not Found error was encountered while trying to use an ErrorDocument to handle the request.
Boston Dynamics
Steve Lohr
Watson, can you grow into a multibillion-dollar business and become the engine of IBM’s resurgence?
IBM is betting its future that the answer is yes. Its campaign to commercialize Watson, the company’s version of artificial intelligence technology, stands out, even during the current A.I. frenzy in the tech industry.
IBM has invested billions of dollars in its Watson business unit, created at the start of 2014, which now employs an estimated 10,000 workers.
**
At the University of North Carolina School of Medicine, Watson was tested on 1,000 cancer diagnoses made by human experts. In 99 percent of them, Watson recommended the same treatment as the oncologists.
In 30 percent of the cases, Watson also found a treatment option the human doctors missed. Some treatments were based on research papers that the doctors had not read — more than 160,000 cancer research papers are published a year. Other treatment options might have surfaced in a new clinical trial the oncologists had not yet seen announced on the web.
But Watson read it all. “Humans enabled by A.I. is the way to go with genomics,” said Dr. Norman E. Sharpless, head of the school’s cancer center.
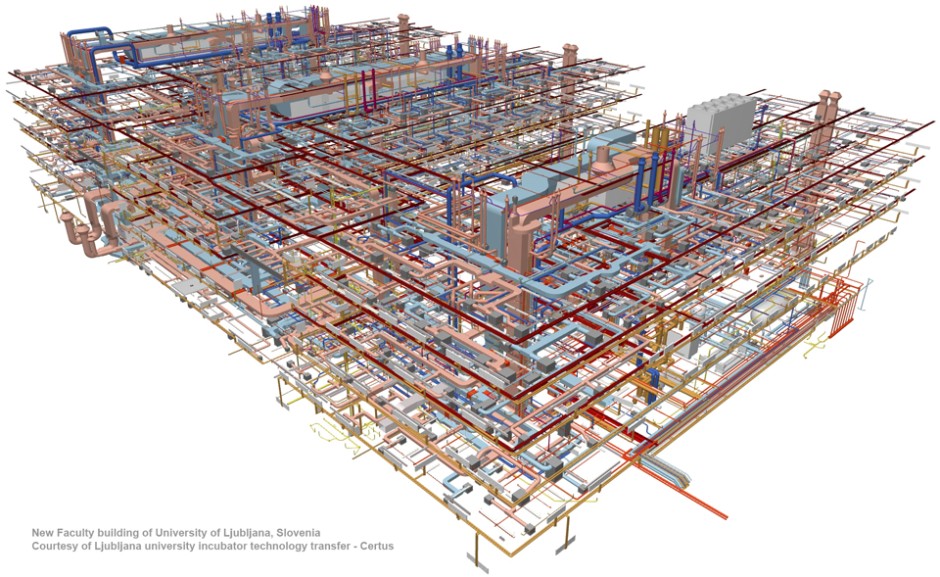
Graphisoft
山梨知彦
 コンピュテーショナルデザインを実務で実践したいと思ったときに、いかにもといった「奇天烈な形状」を生み出すことに抵抗を感じていた。それでコンピュテーショナルな手法でナチュラルなランドスケープをデザインすることを思いついた。「NBF大崎ビル(ソニーシティ大崎)」のランドスケープがそれだ。
コンピュテーショナルデザインを実務で実践したいと思ったときに、いかにもといった「奇天烈な形状」を生み出すことに抵抗を感じていた。それでコンピュテーショナルな手法でナチュラルなランドスケープをデザインすることを思いついた。「NBF大崎ビル(ソニーシティ大崎)」のランドスケープがそれだ。
簡単に言えば、コンピューターのバーチャルな地形の中に、まず人為的にデザインされた植栽計画をする。それをコンピューターの中で、植物相互の近接性や、日照条件、通風条件などを反映して淘汰された状況をシミュレーションする。園路は、植物を愛し、植物の根元を避け、人間に歩きやすいルートを探す仮想の獣を配して、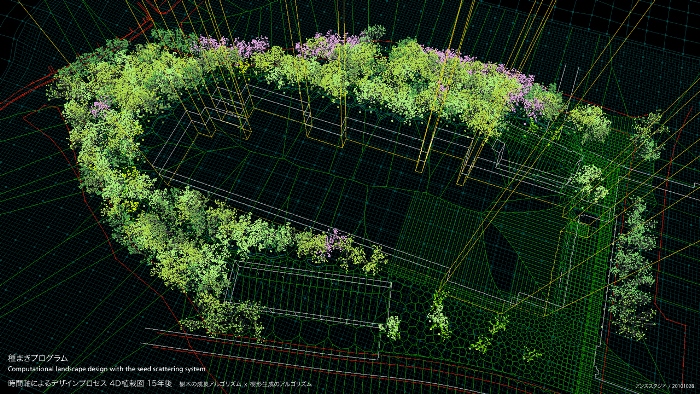 それが踏み固めたルートを採用する。コンピューターの中で40年ほど育ててみて、具合のいい風景が生じたスキームがあったら、その40年後のナチュラルに見える状態を、実際の敷地に張り付けるというデザイン手法である。
それが踏み固めたルートを採用する。コンピューターの中で40年ほど育ててみて、具合のいい風景が生じたスキームがあったら、その40年後のナチュラルに見える状態を、実際の敷地に張り付けるというデザイン手法である。
Center For Medical Simulation
Yahoo
Nikhil Chakravarthi
Mohammad AQib
A user would never like to enter its data or information in the website if he/she feels that it would be insecure. Any unauthorized access may lead to identity theft which may subsequently lead to dire consequences. So the main problems associated with the website can be named as:
1. Loss of control: The user has to rely on the provider to ensure data security and privacy, resource availability, monitoring of services and resources.
2. Lack of Trust: Trusting a third party requires taking risks. Basically trust and risk are the opposite sides of the same coin. Some monitoring or auditing capabilities would be required to increase the level of trust.
Another key challenge is related to cost. As a general rule, the costs of managing user identities should be as low as possible to ensure a reasonable return on investment in the website.
Surrey NanoSystems
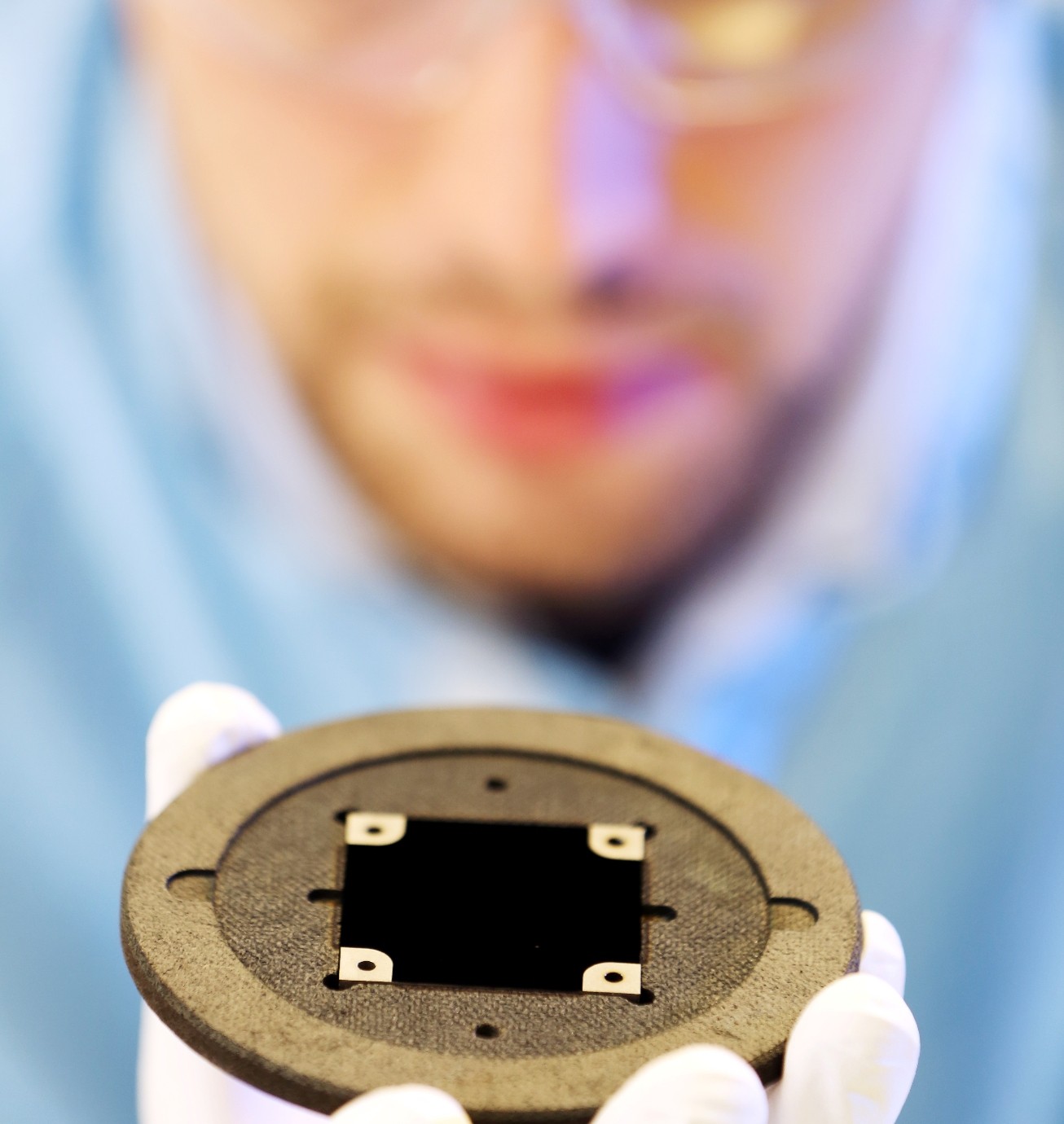 A whole range of products can now take advantage of Vantablack’s astonishing characteristics, thanks to the development of a new spray version of the world’s blackest coating material. The new substance, Vantablack S-VIS, is easily applied at large scale to virtually any surface, whilst still delivering the proven performance of Vantablack.
A whole range of products can now take advantage of Vantablack’s astonishing characteristics, thanks to the development of a new spray version of the world’s blackest coating material. The new substance, Vantablack S-VIS, is easily applied at large scale to virtually any surface, whilst still delivering the proven performance of Vantablack.
Vantablack‘s nano-structure absorbs virtually all incident light, enabling the performance of precision optical systems to be optimized. The material’s developer, UK-based Surrey NanoSystems, has mimicked the performance of its original Vantablack with a new version that can be sprayed onto objects, rather than deposited using a chemical vapor deposition (CVD) process.
Vantablack S-VIS greatly widens the potential applications space, making it possible to coat larger complex shapes and structures. It is applied at temperatures that are easily withstood by common plastics, further extending its use. Even though the material is applied using a simple spraying process, it traps a massive 99.8% of incident light. This property gives Vantablack S-VIS its ability to make objects appear to be two-dimensional black holes, as it becomes impossible to make-out surface topography.
Aaron Sheldrick, Minami Funakoshi
Five years ago, one of the worst earthquakes in history triggered a 10-metre high tsunami that crashed into the Fukushima Daiichi nuclear power station causing multiple meltdowns.
Today, the radiation at the Fukushima plant is still so powerful it has proven impossible to get into its bowels to find and remove the extremely dangerous blobs of melted fuel rods.
The plant’s operator, Tokyo Electric Power Co (Tepco) , has made some progress, such as removing hundreds of spent fuel roads in one damaged building. But the technology needed to establish the location of the melted fuel rods in the other three reactors at the plant has not been developed.
The fuel rods melted through their containment vessels in the reactors, and no one knows exactly where they are now. This part of the plant is so dangerous to humans, Tepco has been developing robots, which can swim under water and negotiate obstacles in damaged tunnels and piping to search for the melted fuel rods.
But as soon as they get close to the reactors, the radiation destroys their wiring and renders them useless.
HTML
────── どうやったら途切れない線になるのか?
──────(罫線)
————— (—)
––––– (–)
――――― (―)
――――― (―)
(<s title=”———————”> </s>)
Boston Dynamics
Defense Industry Daily
 The USA’s MIM-104 Phased Array Tracking Radar Intercept On Target (PATRIOT) anti-air missile system offers an advanced backbone for medium-range air defense, and short-range ballistic missile defense, to America and its allies. This article covers domestic and foreign purchase requests and contracts for Patriot systems. It also compiles information about the engineering service contracts that upgrade these systems, ensure that they continue to work, and integrate them with wider command and defense systems.
The USA’s MIM-104 Phased Array Tracking Radar Intercept On Target (PATRIOT) anti-air missile system offers an advanced backbone for medium-range air defense, and short-range ballistic missile defense, to America and its allies. This article covers domestic and foreign purchase requests and contracts for Patriot systems. It also compiles information about the engineering service contracts that upgrade these systems, ensure that they continue to work, and integrate them with wider command and defense systems.
The Patriot missile franchise’s future appears assured. At present, 12 nations have chosen it as a key component of their air and missile defense systems: the USA, Germany, Greece, Japan, Israel, Kuwait, The Netherlands, Saudi Arabia, South Korea, Spain, Taiwan and the UAE. Poland, Qatar, and Turkey have all indicated varying levels of interest, and some existing customers are looking to upgrade their systems.
Fraunhofer Institute
 When it comes to deciding whether or not the whole of the ball passed over the line, the human eye can be inadequate. Our GoalRef™ goal-line technology supports referees by informing them immediately when a goal is scored.
When it comes to deciding whether or not the whole of the ball passed over the line, the human eye can be inadequate. Our GoalRef™ goal-line technology supports referees by informing them immediately when a goal is scored.
In answering the question of ‘Goal or no goal?’, FIFA will in future be turning to the GoalRef™ goal-line technology developed by the Fraunhofer Institute for Integrated Circuits IIS. After successfully completing a demanding certification process, the GoalRefTM system was officially licensed by FIFA in November 2012, which means it is approved for use at official football matches. Since GoalRefTM produces a reliable decision immediately, it does not interrupt play or alter the character of the game.
Henrik Mkhitaryan, Footbonaut Machine
Andy Greenberg
I was driving 70 mph on the edge of downtown St. Louis when the exploit began to take hold.
Though I hadn’t touched the dashboard, the vents in the Jeep Cherokee started blasting cold air at the maximum setting, chilling the sweat on my back through the in-seat climate control system. Next the radio switched to the local hip hop station and began blaring Skee-lo at full volume. I spun the control knob left and hit the power button, to no avail. Then the windshield wipers turned on, and wiper fluid blurred the glass.
As I tried to cope with all this, a picture of the two hackers performing these stunts appeared on the car’s digital display: Charlie Miller and Chris Valasek, wearing their trademark track suits. A nice touch, I thought.
The Jeep’s strange behavior wasn’t entirely unexpected. I’d come to St. Louis to be Miller and Valasek’s digital crash-test dummy, a willing subject on whom they could test the car-hacking research they’d been doing over the past year. The result of their work was a hacking technique—what the security industry calls a zero-day exploit—that can target Jeep Cherokees and give the attacker wireless control, via the Internet, to any of thousands of vehicles. Their code is an automaker’s nightmare: software that lets hackers send commands through the Jeep’s entertainment system to its dashboard functions, steering, brakes, and transmission, all from a laptop that may be across the country.
cocoa motors
Oliver Chanarin
Technology is always ideological.
U.S. Department of Defense
The Active Denial System (ADS) is needed because it’s the first non-lethal, directed-energy, counter-personnel system with an extended range greater than currently fielded non-lethal weapons. Most counter-personnel non-lethal weapons use kinetic energy (rubber rounds, bean bags, etc.). A kinetic-based system has a higher risk of human injury, and its effectiveness varies in relation to the size, age and gender of the target. The Active Denial System, however, is consistently effective regardless of size, age and gender and has a range greater than small-arms range. The Active Denial System will provide military personnel with a non-lethal weapon that has the same effect on all human targets.
Lely
Margaret Atwood
Every technology we develop is an extension of one of our own senses or capabilities. It has always been that way. The spear and the arrow extended the arm, the telescope extended the eye, and now the Kissinger kissing device extends the mouth. Every technology we’ve ever made has also altered the way we live. So how different will our lives be if the future we choose is the one with all these robots in it?
More to the point, how will we power that future? Every modern robotic form that exists, and every one still to come, depends on a supply of cheap energy. If the energy disappears, so will the robots. And, to a large degree, so will we, since the lifestyle we have built and come to depend on floats on a sea of electricity.
Centre for Process Innovation
Mary Landesman
Trojans have the same right on the system as does the logged in user. In other words, if the user can, the Trojan can. This includes deleting or modifying files, installing other software, uninstalling software, or sending sensitive password and login information to a remote attacker.
Regardless of how the infection gets on the system, once installed, the system is under the control of the attacker. Often, the attacker will share the list of zombied systems with others, giving unfettered access to their collection of zombie machines by other ill-intended criminals. Attackers can also often simply scan for compromised machines, which often send a greeting of readiness to listening ears. Collectively, the zombied systems are referred to as a botnet.
These botnets are then used for a variety of criminal purposes all of which pose serious risk to the infected user as well as the entire Internet community.
Stephen Chen
 China has moved a step closer to creating a supersonic submarine that could travel from Shanghai to San Francisco in less than two hours.
China has moved a step closer to creating a supersonic submarine that could travel from Shanghai to San Francisco in less than two hours.
New technology developed by a team of scientists at Harbin Institute of Technology’s Complex Flow and Heat Transfer Lab has made it easier for a submarine, or torpedo, to travel at extremely high speeds underwater.
In theory, a supercavitating vessel could reach the speed of sound underwater, or about 5,800km/h, which would reduce the journey time for a transatlantic underwater cruise to less than an hour, and for a transpacific journey to about 100 minutes.
However, supercavitation technology has faced two major problems. First, the submerged vessel has needed to be launched at high speeds, approaching 100km/h, to generate and maintain the air bubble.
Second, it is extremely difficult – if not impossible – to steer the vessel using conventional mechanisms, such as a rudder, which are inside the bubble without any direct contact with water.
As a result, its application has been limited to unmanned vessels, such as torpedoes, but nearly all of these torpedoes were fired in a straight line because they had limited ability to turn.
The team of Chinese scientists had found an innovative means of addressing both problems.
Ellen Ullman
I HAVE NO IDEA WHAT TIME IT IS. There are no windows in this office and no clock, only the blinking red LED display of a microwave, which flashes 12:00, 12:00, 12:00, 12:00. Joel and I have been programming for days. We have a bug, a stubborn demon of a bug. So the red pulse no-time feels right, like a read-out of our brains, which have somehow synchronized themselves at the same blink rate.
But what if they select all the text and / hit Delete. / Damn! The NULL case! / And if not were out of the text field and they hit space / yeah, like for / no parameter / Hell! / So what if we space-pad? / I dont know . Wait a minute! / Yeah, we could space-pad / and do space as numeric. / Yes! Well call SendKey(space) to? / the numeric object. / My God! That fixes it! / Yeah! That’ll work if / space is numeric! / if space is numeric!
We lock eyes. We barely breathe. For a slim moment, we are together in a universe where two human beings can simultaneously understand the statement if space is numeric!
Jodi Kantor
Like increasing numbers of low-income mothers and fathers, Ms. Navarro is at the center of a new collision that pits sophisticated workplace technology against some fundamental requirements of parenting, with particularly harsh consequences for poor single mothers. Along with virtually every major retail and restaurant chain, Starbucks relies on software that choreographs workers in precise, intricate ballets, using sales patterns and other data to determine which of its 130,000 baristas are needed in its thousands of locations and exactly when. Big-box retailers or mall clothing chains are now capable of bringing in more hands in anticipation of a delivery truck pulling in or the weather changing, and sending workers home when real-time analyses show sales are slowing. Managers are often compensated based on the efficiency of their staffing.
Scheduling is now a powerful tool to bolster profits, allowing businesses to cut labor costs with a few keystrokes.
Yet those advances are injecting turbulence into parents’ routines and personal relationships, undermining efforts to expand preschool access, driving some mothers out of the work force and redistributing some of the uncertainty of doing business from corporations to families, say parents, child care providers and policy experts.
Toyota
Sales of Fuel Cell sedan will begin in Japan before April 2015 where hydrogen stations are in place.
Preparations are underway for sales to begin in the US and Europe during the summer of 2015.
 It is a vehicle equipped with a “Fuel Cell” that generates electricity through the chemical reaction between hydrogen and oxygen to power the motor driving the vehicle. Hydrogen, which replaces gasoline as fuel, is an environment-friendly energy source that can be produced from various raw materials.
It is a vehicle equipped with a “Fuel Cell” that generates electricity through the chemical reaction between hydrogen and oxygen to power the motor driving the vehicle. Hydrogen, which replaces gasoline as fuel, is an environment-friendly energy source that can be produced from various raw materials.
朝日弘行
三菱重工業は、防衛省の委託を受けて研究開発を進めているステルス戦闘機の試作機を、来年1月に初飛行させる方針を固めた。国内企業による初のステルス戦闘機開発で、防衛省は性能やコストを確認した上で、実用化するかどうか2018年度までに最終判断する方針だ。
ステルス機は中国やロシアが既に試作機を飛行させるなど開発を進めている。日本も09年に、世界最高のステルス性を備えた米国のF22の導入を目指したが、情報流出を警戒する米国の禁輸措置で断念した。このため、防衛力の強化には独自技術の蓄積が必要と判断。国内企業の戦闘機生産も、日米で共同開発した戦闘機F2全94機の生産が11年に完了してから途絶えており、国内防衛産業の生産基盤や技術の維持、向上を図る狙いもある。
政府は00年度以降、ステルス技術の研究に着手。09年度からは、総事業費392億円をかけて試作機の開発を進めていた。試作機のステルス関連技術はすべて三菱重工業など国内企業が開発。敵のレーダーから届いた電波を真っすぐに反射して探知されないよう、機体や外板接合面の形状を設計した。
航空自衛隊に配備予定の最新鋭ステルス機F35(米ロッキード・マーチン社製)はレーダー上で直径10センチほどの物体として認識されるとされ、試作機もこれと同水準の性能を目指している。IHIや富士重工業なども、エンジンや主翼などの主要部材を受け持つ。
三菱重工がエンジンやシステムの作動テスト、基本的な飛行試験などを行った上で、来年3月末までに防衛省に機体を引き渡す。同省は15年度から2年間かけて実戦を想定した試験飛行を重ね、ステルス性や飛行性能を詳しく検証する方針。航空自衛隊が保有する戦闘機のうち、F2が30年代ごろから退役するため、後継機の選択肢に国産ステルス機を加えたい考えだ。
東京大学
Mark Weiser
The most profound technologies are those that disappear. They weave themselves into the fabric of everyday life until they are indistinguishable from it.
ギノ
paizaとは、オンラインのコーディングテストを受ける事で、書類選考なしに面接・会社見学可能な求人企業が見つかる転職サービスです。paizaのコーディングテストは Java, C, C++, C#, PHP, Ruby, Python, Perl に対応しており、より実務に近い試験になっています。

IT/WEB開発エンジニアに特化
エンジニアとしてスペシャリストキャリアを目指す方に特化した求人サービスを展開。
コーディング力をスコアリング
Paizaのコーディングチャレンジでスキルをスコア評価。スキルの強化ポイントを把握。
効率的なマッチングの仕組み
コーディング評価結果を元に、求人企業様が求めるスキル基準と効率的にマッチング。
水野雄二
 DatabaseとGeometry(幾何学)の頭文字をとってデージー・テクノロジーズとしたのが当社の由来です。
DatabaseとGeometry(幾何学)の頭文字をとってデージー・テクノロジーズとしたのが当社の由来です。
『ビジネスアプリによるデータ処理「D」と、CADの図形処理「G」
というふたつのIT分野に特化して会社を運営したい』という思いが込められています。
弊社ではオブジェクト指向技術に基づいたシステム実装技術を得意としており、
多くのプロジェクトで大手企業からも高い評価を得てまいりました。
日本のIT産業において高まる開発案件の需要に対応すべく、2012年度までの5年計画として
1>受託開発体制の強化
2>アウトソーシング事業の確立
3>革新的パッケージの開発
これら三本の事業柱を加速度的に成長させます。
得られた財政基盤を基に、新規事業にも積極的に投資していきます。
环球网
ヤマト運輸
Apple
Solid Concepts
Erik Schechter
 Weighing only 16 grams, the Black Hornet looks like a tiny toy helicopter. But it’s really a nano-size piece of military hardware unlike anything on the battlefield today — experimental robot flies and hummingbirds not withstanding.
Weighing only 16 grams, the Black Hornet looks like a tiny toy helicopter. But it’s really a nano-size piece of military hardware unlike anything on the battlefield today — experimental robot flies and hummingbirds not withstanding.
The PD-100 Black Hornet Personal Reconnaissance System, unveiled to the American public for the first time last week at the Association of the United States Army Expo in Washington, D.C., is a drone (actually, a pair of them) that a soldier can carry and operate as easily as he or she would a radio.
HyperStealth Biotechnology Corp.
Successful testing yesterday with our Quantum Stealth (light bending material) covering a UAV (Unmanned Aerial Vehicle).
The UAV was able to taking off, fly a course at high speed, return back and land, repeating these tasks multiple times without any apparent change in the flight characteristics of the UAV.
Currently only special authorized groups in the Canadian and U.S. militaries have access to the material and Quantum Stealth has been classified by both countries …
The U.S. Army Research, Development and Engineering Command
Antonov Company
 Mriya has set up 240 world records including transportation of the heaviest cargo with mass of 253 tons, the heaviest single peace of cargo with mass of 186,7 t as well as the longest cargo having length of 42,1 m. But the main thing is that Mriya serves people reliably. The airplane repeatedly participated in humanitarian operations. Thus in October, 2009 the AN-225 performed several flights on delivery generators to Samoa. They were necessary for renewal of work of Satala electric station damaged by tsunami. Only spacious cabin of the AN-225 could accommodate ten 12-tons generators at once. Each of them was as large as 6-meters container.
Mriya has set up 240 world records including transportation of the heaviest cargo with mass of 253 tons, the heaviest single peace of cargo with mass of 186,7 t as well as the longest cargo having length of 42,1 m. But the main thing is that Mriya serves people reliably. The airplane repeatedly participated in humanitarian operations. Thus in October, 2009 the AN-225 performed several flights on delivery generators to Samoa. They were necessary for renewal of work of Satala electric station damaged by tsunami. Only spacious cabin of the AN-225 could accommodate ten 12-tons generators at once. Each of them was as large as 6-meters container.
Boston Dynamics
稲田修一
Alan Webber
 In the end, the location of the new economy is not in the technology, be it the microchip or the global telecommunications network. It is in the human mind.
In the end, the location of the new economy is not in the technology, be it the microchip or the global telecommunications network. It is in the human mind.
You can’t judge great teachers by their looks. Or their English. Or their profession. Or their education. Or where they were born, where they live, how they dress, how much money they make.
Julia White
We have one billion users of Office. You can’t expect them to change every day.
Quentin Hardy
![]() Every day, millions of office workers prepare memos and reports using scissors and paste, and store data on floppy disks, though they have plenty of digital memory in their computers and the cloud. Smartphone-toting executives have their mail dumped into in-boxes, one corporate message atop another.
Every day, millions of office workers prepare memos and reports using scissors and paste, and store data on floppy disks, though they have plenty of digital memory in their computers and the cloud. Smartphone-toting executives have their mail dumped into in-boxes, one corporate message atop another.
They are not using these objects, of course, but clicking on the pictures of them in popular word-processing programs like Microsoft Word or Google Docs. The icons linger like vestigial organs of an old-style office, 31 years after IBM’s personal computer brought work into the software age. They symbolize an old style of office software, built for the time when the desktop computer was new and unfamiliar.
But no longer are workers tethered to a desk, or even to an office; we are all toting around laptops, tablets and smartphones to make every place a workplace. And so office software is changing. These days, what is important is collaboration, small screens, fast turnarounds, social media and, most of all, mobility.
Harold G. White
 Space has been expanding since the Big Bang 13.7 billion years ago. And we know that when you look at some of the cosmology models, there were early periods of the universe where there was explosive inflation, where two points would’ve went receding away from each other at very rapid speeds.
Space has been expanding since the Big Bang 13.7 billion years ago. And we know that when you look at some of the cosmology models, there were early periods of the universe where there was explosive inflation, where two points would’ve went receding away from each other at very rapid speeds.
Nature can do it. So the question is, can we do it?
Anatoly Zak
 Russia’s Proton rocket crashed less than a minute after its liftoff from Baikonur, Kazakhstan on July 2, 2013. The rocket started veering off course right after leaving the pad, deviating from the vertical path in various directions and then plunged to the ground seconds later nose first. The payload section and the upper stage were sheered off the vehicle moments before it impacted the ground and exploded.
Russia’s Proton rocket crashed less than a minute after its liftoff from Baikonur, Kazakhstan on July 2, 2013. The rocket started veering off course right after leaving the pad, deviating from the vertical path in various directions and then plunged to the ground seconds later nose first. The payload section and the upper stage were sheered off the vehicle moments before it impacted the ground and exploded.
By July 9, it is transpired that investigators sifting through the wreckage of the doomed rocket had found critical angular velocity sensors, DUS, installed upside down. Each of those sensors had an arrow that was suppose to point toward the top of the vehicle, however multiple sensors on the failed rocket were pointing downward instead. As a result, the flight control system was receiving wrong information about the position of the rocket and tried to “correct” it, causing the vehicle to swing wildly and, ultimately, crash. The paper trail led to a young technician responsible for the wrong assembly of the hardware, but also raised serious issues of quality control at the Proton’s manufacturing plant, at the rocket’s testing facility and at the assembly building in Baikonur. It appeared that no visual control of the faulty installation had been conducted, while electrical checks could not detect the problem since all circuits had been working correctly.
Dan Brown
(Your novel raises the question of whether technology will save us or destroy us. Which do you believe?)
I believe science will save us…although I tend to be an optimist. Obviously, science has wonderful potential to control disease, create new fuel supplies, engineer efficient food sources, and even allow us to migrate to new worlds. The problem, of course, is that every technology is a double-edged sword. The rocket engine that carries the space shuttle can also carry warheads. The medical breakthroughs that can eradicate disease–genetic research, for example-if misused, can bring about the end of the human race. The question is not whether or not science will expand to meet man’s growing needs, but whether man’s philosophy will mature fast enough that we can truly comprehend our new power and the responsibility that comes with it.
EvoLogics
 Recent studies on the functional morphology of fins of fishes show a surprising biomechanical effect of the fin rays. The bionic implementations of these constructions led to shape-adaptive wing profiles and flow control devices. The functional principle has been patented as “Fin Ray Effect” and a line of products based on this effect is currently being developed.
Recent studies on the functional morphology of fins of fishes show a surprising biomechanical effect of the fin rays. The bionic implementations of these constructions led to shape-adaptive wing profiles and flow control devices. The functional principle has been patented as “Fin Ray Effect” and a line of products based on this effect is currently being developed.
The U.S. Army Research Laboratory
 The U.S. Army Research Laboratory’s (ARL), Army Research Office’s (ARO) initial concept of exploring DNA as a tagging and tracking method has led to the discovery of an optical scanning technology that can identify counterfeit electronic components before they are integrated into Army materiel.
The U.S. Army Research Laboratory’s (ARL), Army Research Office’s (ARO) initial concept of exploring DNA as a tagging and tracking method has led to the discovery of an optical scanning technology that can identify counterfeit electronic components before they are integrated into Army materiel.
The technology also provides the capability to identify and track materiel in the absence of external tags or barcodes.
This timely discovery will help address a significant challenge within the Army and DoD: the presence of counterfeit electronic components in military equipment.
NHK
軽く、かたい「アワビの貝殻」の構造をまねした新素材でつくる宇宙船、炭素繊維より軽く、強く、しなやかな「クモの糸」でつくる自動車のボディー、壁や天井を自在に移動する「ヤモリの足」の仕組みを取り入れた強力な粘着テープ。いま、厳しい生存競争の中で生物が進化させてきた機能を模倣するバイオミメティクス(生物模倣技術)により、革新的な技術が次々と生まれようとしている。電子顕微鏡やナノテクノロジーの進化により、生物の神秘のメカニズムを分子レベルで解明、再現できるようになってきたのだ。次世代技術として期待される一方で、日本では昆虫学や動物学の研究者と工学系の技術者との連携が弱く、製品化の動きは欧米に大きく遅れを取っているのが現状だ。生物のパワーをどう技術開発に生かし、イノベーションにつなげていくのか。
NASA
Spiber
IBM
Микоян МиГ-35
 New modifications include the newly rolled-out Phazotron Zhuk-AE active electronically scanned array (AESA) radar. The Phazotron Zhuk-AE AESA radar offers a wider range of operating frequencies, providing more resistance to electronic countermeasures (ECM), more detection range, more air and ground targets detected, tracked and able to be engaged simultaneously. The radar is thought to have detection range of 160 km (86 nmi) for air targets and 300 km (160 nmi) for ships.
New modifications include the newly rolled-out Phazotron Zhuk-AE active electronically scanned array (AESA) radar. The Phazotron Zhuk-AE AESA radar offers a wider range of operating frequencies, providing more resistance to electronic countermeasures (ECM), more detection range, more air and ground targets detected, tracked and able to be engaged simultaneously. The radar is thought to have detection range of 160 km (86 nmi) for air targets and 300 km (160 nmi) for ships.
Сухой
Northrop Grumman
 Command, Control, Communications, Computers, Intelligence, Surveillance and Reconnaissance – better known as C4ISR. From leading-edge microelectronics to the largest, most complex system-of-systems in the world, Northrop Grumman’s C4ISR breadth, depth and ability provides first responders, intelligence gatherers, decision-makers and military personnel on the front lines the tools necessary to act with speed and confidence.
Command, Control, Communications, Computers, Intelligence, Surveillance and Reconnaissance – better known as C4ISR. From leading-edge microelectronics to the largest, most complex system-of-systems in the world, Northrop Grumman’s C4ISR breadth, depth and ability provides first responders, intelligence gatherers, decision-makers and military personnel on the front lines the tools necessary to act with speed and confidence.
Carlo Kopp
Aerial combat in the coming decades will be dominated by players who have command of information over their opponents, and are able to exploit that advantage offensively. Information has become the new high ground in the game of aerial combat. Globally, and especially in Asia, this has been reflected by sustained high levels of investment in capabilities historically operated only the US and NATO nations, such as AWACS/AEW&C and networking of combat aircraft, AWACS/AEW&C and ground based surveillance systems.
Concurrently we have observed strong investment in counter-ISR systems, intended to render AWACS/AEW&C impotent. Such systems include very long range air to air missiles such as the Russian R-37/AA-13 Arrow and R-172/K-100 intended to destroy AWACS/AEW&C, but also capable ground based jamming systems like the SPN-2/4/30 series, Pelena 1, Topol E and supporting ELINT systems like the Orion/Vega 85V6 series.
Basic technologies determine what kind of airframes, propulsion, systems and weapons can be employed by either side in a conflict. The side with a significant lead in basic technology will prevail, all else being equal, due to the performance and capability gains that lead confers.
Perhaps the most foolish of the popular misconceptions of Russian basic technology is that which assumes that the US and EU maintain the technological lead of 1-2 decades held at the end of the Cold War. Alas, nearly two decades later, in a globalised, digitised and networked world, the US retains a decisive lead only in top end stealth technologies, and some aspects of networking and highly integrated systems software. The Russians have closed the gap in most other areas, but importantly, have mastered the difficult embedded software technology so critical for radar and electronic warfare systems, as well as sensor fusion, networking and engine and flight controls. The Russians are working very hard at closing the remaing gap, with the planned PAK-FA fighter to be properly shaped for low observable and very low observable stealth capability.
The latest Russian MiG-35 Fulcrum F and Su-35-1 Flanker E+ both illustrate this in a very convincing manner.
Steve Scherer
 Italy’s 5-Star Movement, led by comic Beppe Grillo, wants to scrap the country’s planned purchase of 90 Lockheed Martin Corp F-35 fighter jets and use the savings to help boost the struggling economy.
Italy’s 5-Star Movement, led by comic Beppe Grillo, wants to scrap the country’s planned purchase of 90 Lockheed Martin Corp F-35 fighter jets and use the savings to help boost the struggling economy.
Eliminating the purchase of the fighter jets would save Italy a total of an estimated 10 billion euros but it would leave the Air Force and the country’s new aircraft carrier with an outdated fighter fleet.
The troubled F-35 is seven years behind schedule and 70 percent over early cost estimates, and orders for the super technological new jet have been cut during an economic crisis that has shrunk defence budgets worldwide.
Last year, Italy cut its F-35 order to 90 warplanes from the 131 it had agreed to buy more than a decade ago, a move it said would save 5 billion euros. The package also includes maintenance work for Italy’s state controlled defence technology group Finmeccanica.
The 5-Star Movement does not have enough votes in parliament to shoot down the jet purchases on its own, but political momentum against the Joint Strike Fighter is building.
Lt. Col Tom McIntyre
We initially planned for a nine-month mission, which we are roughly at now, but we will continue to extend the mission as circumstances allow. Keeping the X-37 in orbit will provide us with additional experimentation opportunities and allow us to extract the maximum value out of the mission.
We are learning new things about the vehicle every day, which makes the mission a very dynamic process.



CNBC
 Google Glass consists of a small display situated on a frame that resembles eyeglasses. It is connected to a camera, microphone and bone-conducting speaker. Glass pairs with your smartphone wirelessly using Bluetooth, but also can use Wi-Fi to access the Internet. You can use your voice or your finger to get it to take photos, record video, initiate video or voice chats, send messages, search Google and translate words or phrases. Google’s being a bit coy about the ship date for this groundbreaking wearable computer. However, while qualifying early adopters are paying $1,500 a pop for the privilege of owning it first, we’re told that it will become more widely available by year’s end-with a slightly more affordable price tag.
Google Glass consists of a small display situated on a frame that resembles eyeglasses. It is connected to a camera, microphone and bone-conducting speaker. Glass pairs with your smartphone wirelessly using Bluetooth, but also can use Wi-Fi to access the Internet. You can use your voice or your finger to get it to take photos, record video, initiate video or voice chats, send messages, search Google and translate words or phrases. Google’s being a bit coy about the ship date for this groundbreaking wearable computer. However, while qualifying early adopters are paying $1,500 a pop for the privilege of owning it first, we’re told that it will become more widely available by year’s end-with a slightly more affordable price tag.
One of the reasons Glass will find itself unwelcome in places is because its camera lives at the wearer’s eye level. It takes photos or record videos without a red blinking light telling others it’s happening. Anywhere cameras and other recording devices are unwelcome, the same would most certainly go for Google Glass.
For starters, you can forget about taking Glass to Las Vegas. Casinos are another place where surreptitious recording equipment won’t be welcome.
CrossLoop
クロスループは、インストールして接続ボタンを押すだけで、どんなに離れていてもインターネットが接続されていれば画面共有を行い、相手の画面上から相手のパソコンを操作する事が出来るようになるソフトウェアです。
主に現在は、仕事上、家族同士や友人同士のパソコンサポート用に利用されていますが、何にご使用いただくかはお客様のアイデア次第です。
使用可能な言語は日本語を含め、21あり、190カ国の皆様にご使用頂いています。
また画面共有に使用される通信は128ビットのBlowfish技術を用いて暗号化されていますので、また起動のたびに、アクセスコードが変わり、そのアクセスコードを相手に教えないと接続出来ないしくみとなっていますので、セキュリティは万全です。
また、ポートの開放は不要です。