I believe three fundamental problems explain why computational AI has historically failed to replicate human mentality in all its raw and electro-chemical glory, and will continue to fail.
First, computers lack genuine understanding. The Chinese Room Argument is a famous thought experiment by US philosopher John Searle that shows how a computer program can appear to understand Chinese stories (by responding to questions about them appropriately) without genuinely understanding anything of the interaction.
Second, computers lack consciousness. An argument can be made, one I call Dancing with Pixies, that if a robot experiences a conscious sensation as it interacts with the world, then an infinitude of consciousnesses must be everywhere: in the cup of tea I am drinking, in the seat that I am sitting on. If we reject this wider state of affairs – known as panpsychism – we must reject machine consciousness.
Lastly, computers lack mathematical insight. In his book The Emperor’s New Mind, Oxford mathematical physicist Roger Penrose argued that the way mathematicians provide many of the “unassailable demonstrations” to verify their mathematical assertions is fundamentally non-algorithmic and non-computational.
Category Archives: information
Rodney Brooks
Every time we figure out a piece of it, it stops being magical;
we say, “Oh, that’s just a computation.”
Larry Tesler
My formulation of what others have since called the “AI Effect”. As commonly quoted:
Artificial Intelligence is whatever hasn’t been done yet.
What I actually said was:
Intelligence is whatever machines haven’t done yet.
Many people define humanity partly by our allegedly unique intelligence.
Whatever a machine—or an animal—can do must (those people say) be something other than intelligence.
Douglas Hofstadter
It always takes longer than you expect, even when you take into account Hofstadter’s Law.
Guy Mann Dude
 The problem with AI is that it is constantly being redefined. At one point, a robot that would vaccum your house without you lifting a finger would have been considered an example of AI. Nowdays, hardly anyone is impressed by a Roomba. It used to be that a computer that could beat a human grandmaster at chess would have sufficed as AI. Today, we consider that to be little more than a clever computer algorithm. AI will always be 10+ years away if we keep redefining it to exclude any successes we achieve.
The problem with AI is that it is constantly being redefined. At one point, a robot that would vaccum your house without you lifting a finger would have been considered an example of AI. Nowdays, hardly anyone is impressed by a Roomba. It used to be that a computer that could beat a human grandmaster at chess would have sufficed as AI. Today, we consider that to be little more than a clever computer algorithm. AI will always be 10+ years away if we keep redefining it to exclude any successes we achieve.
Fabio Assolini
To help new ‘entrepreneurs’ or beginners interested in a life of cybercrime, some Brazilian bad guys started to offer paid courses. Others went even further, creating a Cybercrime school to sell the necessary skills to anyone who fancies a life of computer crime but lacks the technical know-how.
A number of different courses are offered, and while some seem like legitimate ones — how to become a designer, a Web designer, a hacker, a programmer — others not so much as they offer to teach how to become a ‘banker,’ a defacer or a spammer,
Cathy O’Neil
The math-powered applications powering the data economy were based on choices made by fallible human beings. Some of these choices were no doubt made with the best intentions. Nevertheless, many of these models encoded human prejudice, misunderstanding, and bias into the software systems that increasingly managed our lives. Like gods, these mathematical models were opaque, their workings invisible to all but the highest priests in their domain: mathematicians and computer scientists. Their verdicts, even when wrong or harmful, were beyond dispute or appeal. And they tended to punish the poor and the oppressed in our society while making the rich richer.
Cathy O’Neil
For many of the businesses running these rogue algorithms, the money pouring in seems to prove and it makes sense. When they’re building statistical systems to find customers or manipulate desperate borrowers, growing revenue appears to show that they’re on the right track. The software is doing its job. The trouble is that profits end up serving as a stand-in, or proxy, for truth.
This happens because data scientists all too often lose sight of the folks on the receiving end of the transaction. They certainly understand that a data-crunching program is bound to misinterpret people a certain percentage of the time, putting them in the wrong groups and denying them a job or a chance at their dream house. But as a rule, the people running the WMDs don’t dwell on those errors. Their feedback is money, which is also their incentive. Their systems are engineered to gobble up more data and fine-tune their analytics so that more money will pour in. Investors, of course, feast on these returns and shower WMD companies with more money.
Michael Burrows, Jeffrey A. Dean
Document treadmilling system and method for updating documents in a document repository and recovering storage space from invalidated documents
A tokenspace repository stores documents as a sequence of tokens. The tokenspace repository, as well as the inverted index for the tokenspace repository, uses a data structure that has a first end and a second end and allows for insertions at the second end and deletions from the front end. A document in the tokenspace repository is updated by inserting the updated version into the repository at the second end and invalidating the earlier version. Invalidated documents are not deleted immediately; they are identified in a garbage collection list for later garbage collection. The tokenspace repository is treadmilled to shift invalidated documents to the front end, at which point they may be deleted and their storage space recovered.
Internet Live Stat
Google now processes over 73,000 search queries every second on average, which translates to over 6.3 billion searches per day and 2.3 trillion searches per year worldwide.
Jennifer Valentino-Devries, Natasha Singer, Michael H. Keller, Aaron Krolik
Apps form the backbone of this new location data economy.
The app developers can make money by directly selling their data, or by sharing it for location-based ads, which command a premium. Location data companies pay half a cent to two cents per user per month.
Targeted advertising is by far the most common use of the information.
Google and Facebook, which dominate the mobile ad market, also lead in location-based advertising. Both companies collect the data from their own apps. They say they don’t sell it but keep it for themselves to personalize their services, sell targeted ads across the internet and track whether the ads lead to sales at brick-and-mortar stores. Google, which also receives precise location information from apps that use its ad services, said it modified that data to make it less exact.
Smaller companies compete for the rest of the market, including by selling data and analysis to financial institutions. This segment of the industry is small but growing, expected to reach about $250 million a year by 2020.
Apple and Google have a financial interest in keeping developers happy, but both have taken steps to limit location data collection. In the most recent version of Android, apps that are not in use can collect locations “a few times an hour,” instead of continuously.
Apple has been stricter, for example requiring apps to justify collecting location details in pop-up messages.
Jennifer Valentino-Devries, Natasha Singer, Michael H. Keller, Aaron Krolik
Your apps know where you were last night, and they’re not keeping it secret.
Dozens of companies use smartphone locations to help advertisers and even hedge funds. They say it’s anonymous, but the data shows how personal it is.

Data reviewed by The Times shows over 235 million locations captured from more than 1.2 million unique devices during a three-day period in 2017.
永安悟史
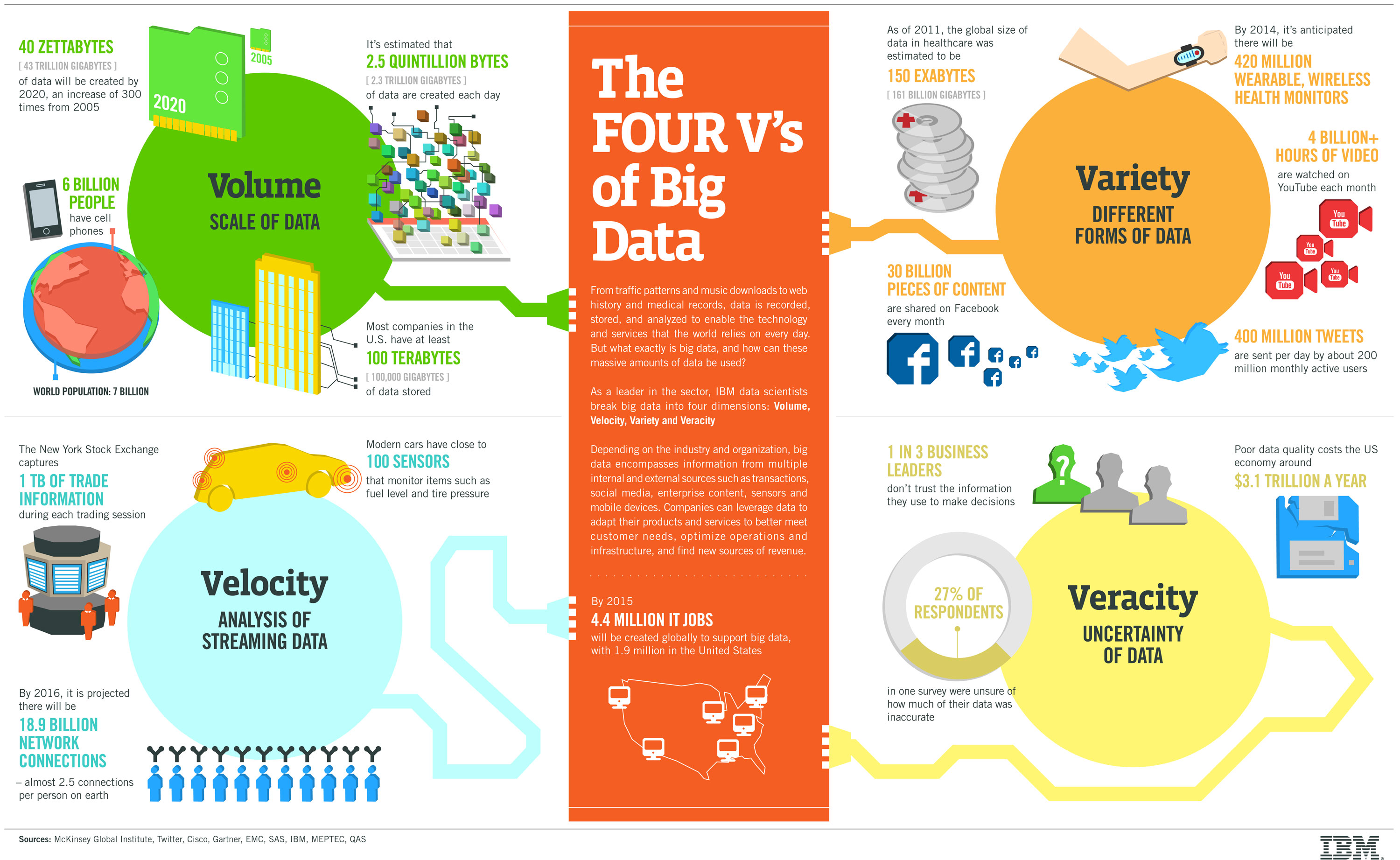
コモディティサーバを使ってスケールアウトさせる、ストレージからデータを取り出して処理するのではなく、データのあるところ(ノード)で処理させるというHadoopの思想は、「増え続けるVolumeに如何に対応するか」という問題意識が出発点になっていたように思います。
そのため、Hadoop以降のデータ処理に関連するハードウェアやソフトウェアは、まずはこのVolumeへの対応力を高めるところにフォーカスして開発され、扱えるデータサイズや処理のスループットなどが競われてきました。テクノロジーとしてはMap-Reduce(バッチ)からMPPまで、さまざまなテクノロジーが存在しており、この10年ほどの間にそれぞれのテクノロジーが進歩してきました。
その結果として「Volume」への対応力はテクノロジーの進歩とともに非常に高まってきたと思います。私自身、現在はExadataのユーザですし、周りにはHadoopユーザも多くいますが、数千万、億単位のレコードのテーブルを処理するのは当たり前、というような日々になりつつあります。一昔前と比べると大容量のデータを処理するテクノロジーは大きく発達して、身近に、かつ使いやすくなってきました。
「Volume」への対応力はテクノロジーの進歩が大きく貢献した領域と言えますし、この認識を否定する人はあまりいないでしょう。
Srinath Perera
Big data established the value of insights derived from processing data. Such insights are not all created equal. Some insights are more valuable shortly after it has happened with the value diminishes very fast with time. Stream Processing enables such scenarios, providing insights faster, often within milliseconds to seconds from the trigger.
Bruce Ratner
The regression theoretical foundation and the tool of significance testing employed on big data are without statistical binding force. Thus, fitting big data to a prespecified small-framed model produces a skewed model with doubtful interpretability and questionable results.
Kevin Fink
 It is not uncommon to be handed a dataset without a lot of information as to where it came from, how it was collected, what the fields mean, and so on. In fact, it’s probably more common to receive data in this way than not. In many cases, the data has gone through many hands and multiple transformations since it was gathered, and nobody really knows what it all means anymore.
It is not uncommon to be handed a dataset without a lot of information as to where it came from, how it was collected, what the fields mean, and so on. In fact, it’s probably more common to receive data in this way than not. In many cases, the data has gone through many hands and multiple transformations since it was gathered, and nobody really knows what it all means anymore.
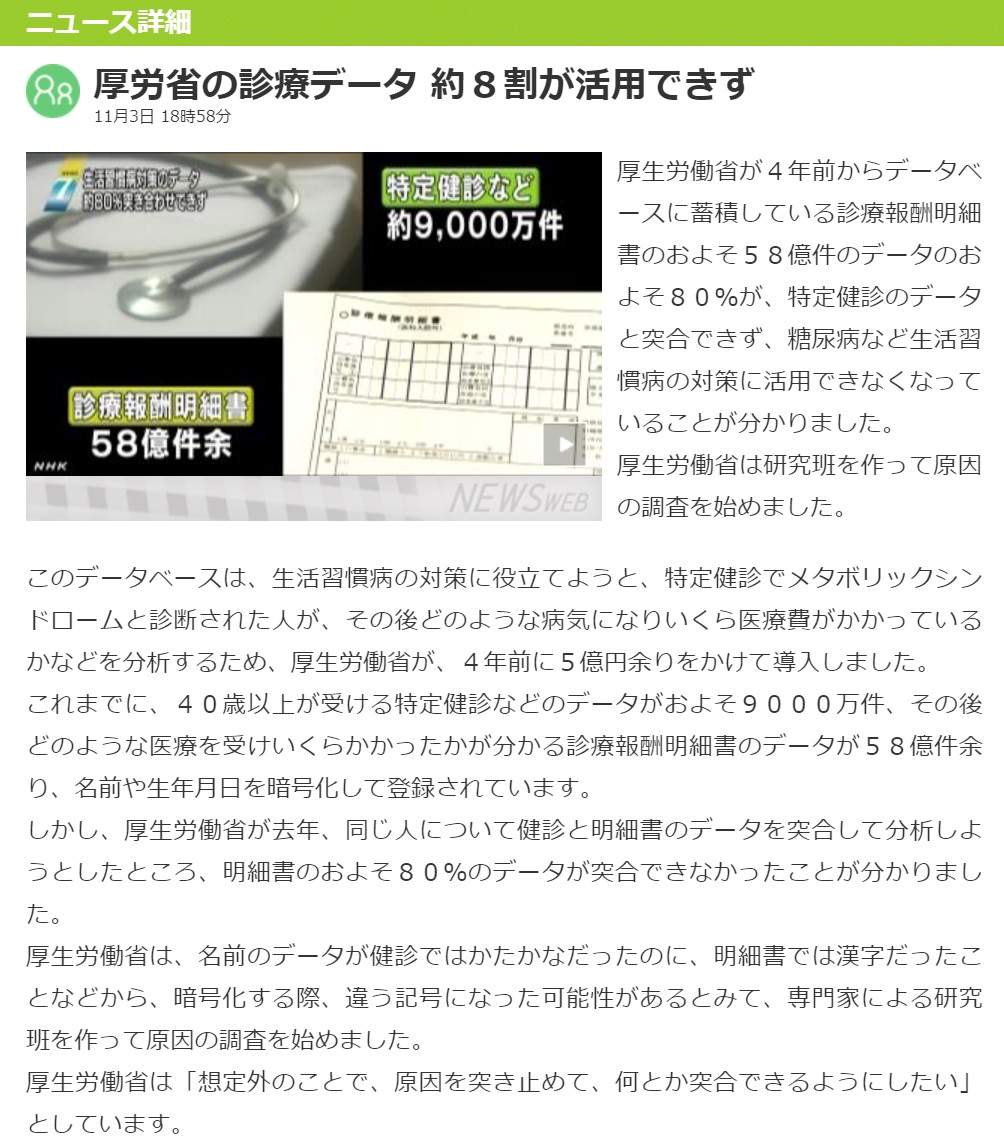
NHK
IBM
中原淳
わたしたちの世界は、データが直接リアルな現場を変えるのではなく、現場にいる人間にデータが解釈され、意味づけられたときに、現場を変えるのです。この「解釈」や「意味づけ」を軽視してはいけません。ところが今は、「データがあれば、現場が変わる」とか「データそのものが現実を変えることができる」と声高に叫ぶような論調がすごく多い。これは素朴すぎる科学主義だし、データ万能主義に陥っているといえます。
John Snow
Neither Shodan nor Censys are likely to be used by some serious cybercriminals — the real big bad guys have had botnets for a while, which can serve the very same purpose yet yield more power. It took Shodan’s creator John Matherly only 5 hours to ping and map all the devices on the whole Internet, and a botnet utilising hundreds of computers would probably do that even faster.
But there are a lot of other people who already have tried to misuse Shodan and Censys to play bad tricks and pranks on other people.
Censys
Devin Coldewey
The security lapse was discovered by Victor Gevers at the GDI Foundation, a security organization working in the public’s interest. Using the infamous but useful Shodan search engine, he found a MongoDB instance owned by the Chinese company SenseNets that stored an ever-increasing number of data points from a facial recognition system apparently at least partially operated by the Chinese government.
Many of the targets of this system were Uyghur Muslims, an ethnic and religious minority in China that the country has persecuted in what it considers secrecy, isolating them in remote provinces in what amount to religious gulags.
This database was no limited sting operation: some 2.5 million people had their locations and other data listed in it. Gevers told me that data points included national ID card number with issuance and expiry dates; sex; nationality; home address; DOB; photo; employer; and known previously visited face detection locations.
Devin Coldewey
For the first time in history, people have a way of securing their communications quickly, automatically, and at will from any threat, be it hackers or government snoops.
Good for us — but for the FBI and the police, it’s a calamity. Where once they could pry open locked drawers to find incriminating letters, or force a company to reveal private records, now everything depends on the willingness of the owner to allow that information to be decrypted.
Since they can’t go through the front door, so to speak, they have asked repeatedly for a back door. But what exactly is a backdoor, and why should you care?
The concept of a backdoor is simple to state but not so simple to definitively pin down. Like the back door of a house, a crypto backdoor (generally written as a single word) is a way to circumvent the locks and protections of the main entrance in order to walk in unobstructed and make oneself comfortable. A backdoor could be in a phone, laptop, router, security camera — any device, really.
Devin Coldewey
Because AI is so poorly defined, it’s really easy to say your device or service has it and back that up with some plausible-sounding mumbo jumbo about feeding a neural network a ton of data on TV shows or water use patterns.
Devin Coldewey
Intelligence is the ability to solve new problems.
That, after all, is really what is at the heart of the “adaptability,” the “generalizing,” the “initiative” that alloys alternately the “reason,” “judgment,” or “perception” abundant in the intelligent mind. Clearly it is important that one is able to solve problems, to reason one’s way through the world — but more important than that, one must be able to turn the ability to solve some problems into the ability to solve other problems. That transformative nature is key to intelligence, even if no one is quite sure how to formalize the idea.
Will our AIs one day be imbued with this all-important adaptable reason, and with it slip the leash, turning to new problems never defined or bounded by their creators?
みんなの経済新聞
足立経済新聞 すみだ経済新聞 深川経済新聞 浅草経済新聞 アキバ経済新聞 神田経済新聞 日本橋経済新聞 銀座経済新聞 新橋経済新聞 品川経済新聞 東京ベイ経済新聞 六本木経済新聞 赤坂経済新聞 市ケ谷経済新聞 池袋経済新聞 赤羽経済新聞 板橋経済新聞 練馬経済新聞 高田馬場経済新聞 新宿経済新聞 中野経済新聞 高円寺経済新聞 下北沢経済新聞 三軒茶屋経済新聞 二子玉川経済新聞 自由が丘経済新聞 目黒経済新聞 シブヤ経済新聞 吉祥寺経済新聞 調布経済新聞 北多摩経済新聞 立川経済新聞 八王子経済新聞 町田経済新聞 西多摩経済新聞 石垣経済新聞 台北経済新聞 香港経済新聞 ホーチミン経済新聞 バンコク経済新聞 シンガポール経済新聞 バリ経済新聞 マニラ経済新聞 ドバイ経済新聞 ニューヨーク経済新聞
Frédéric Joignot
En avril 1993, Tim Berners-Lee obtient du prestigieux laboratoire européen qu’il enregistre le nouvel outil dans le domaine public, publie son code source et l’ouvre au « réseau des réseaux » mondial en gestation, l’Internet. Il est persuadé que le « véritable potentiel » du Web ne peut être libéré que s’il devient « un espace universel » où n’importe qui, en n’importe quel lieu, peut aller chercher librement des ressources, cela « gratuitement » et « sans permission ».
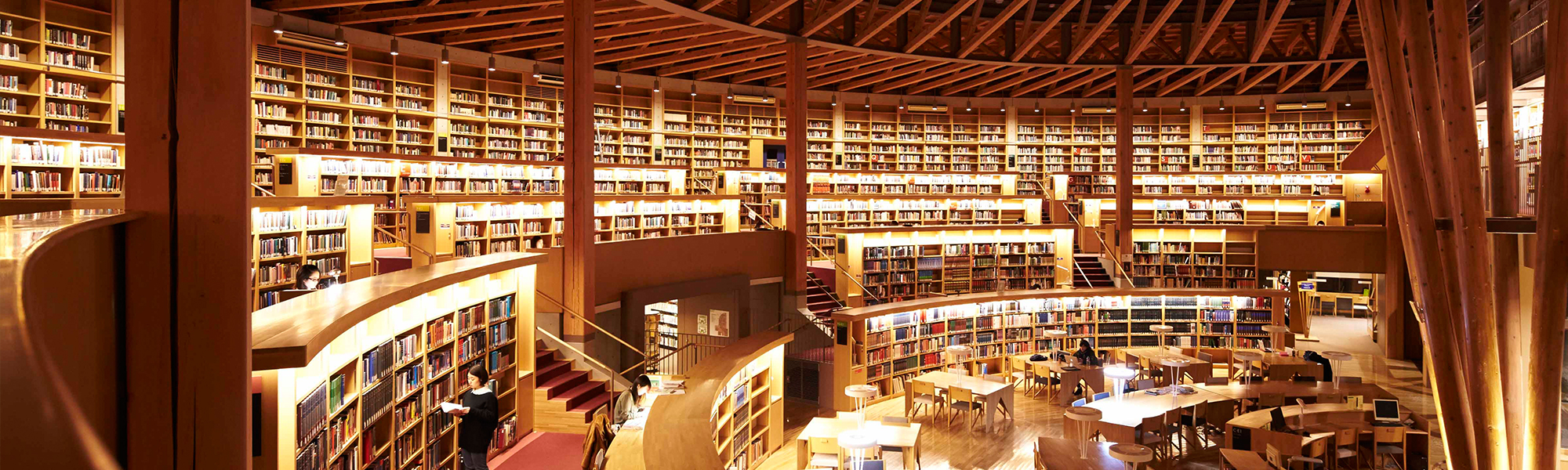
Il pressent qu’un des plus vieux rêves de l’humanité – rassembler toute la connaissance connue dans un espace que tous puissent explorer, une utopie qui remonte à la bibliothèque d’Alexandrie (fondée par Ptolémée en 288 av. J.-C.) et passe par l’imprimerie de Johannes Gutenberg (1400-1468) – devient possible, à la croisée du Web et d’Internet, et pense qu’il doit être offert au monde.
Michael Beckerman
Fewer than five clicks. That’s all it takes to change privacy settings on your favorite social media or streaming service.
Online platforms, unlike most traditional business, proactively create contextual tools that help people better understand and control their privacy settings. Contrast that with cellphone carriers selling our location to bounty hunters or magazine publishers selling our subscription information to data brokers.
Companies across every sector of the economy collect and use consumer data. That’s why we support an economywide federal privacy law that requires real transparency and meaningful control over how data is collected, used and shared.
Stephen Covey
Between stimulus and response there is a space. In that space is our power to choose our response. In our response lies our growth and our freedom.
Ask HN (Hacker News)
With the sheer amount of information available in the world today I have simply become overwhelmed. My mind is in a constant racing state. It’s calm but not calm if that makes sense. While I could very well be thinking about nothing or something specific like writing this message. My mind seems to have multiple levels. One of which is directed to what I am actively doing and one below it which seems to process information in a never ending manner. I am not actively thinking about these things but it’s there. Articles and books to read, shows to watch, things to do in my personal life and at work. Career advancement. All of these things just never stop but I could be calm. I can sleep fine, they don’t cause active anxiety. They just linger in the background. Shooting around saying me me.
It’s getting exhausting.
Julia Kho
The Central Limit Theorem (CLT) states that the sampling distribution of the mean of any independent, random variable will be normal or nearly normal, if the sample size is large enough.
In other words, if we take enough random samples that are big enough, the proportions of all the samples will be normally distributed around the actual proportion of the population. Note that the underlying sample distribution does not have to be normally distributed for the CLT to apply. To break this down even further, imagine collecting a sample and calculating the sample mean. Repeat this over and over again, collecting a new, independent sample from the population each time. If we plotted a histogram of each sample mean, the distribution will be normally distributed.
Open Data Science Conference (ODSC)
- What is the significance of the normal distribution to data science?
- Tell me about your passion for data science. Do you: attend local meetups, participate in data challenges like Kaggle, work to use data for common good like public data hacking, speak at conferences, write books or articles, etc.?
- Describe that last time you experienced frustration in a data science project you were working on, and how did you overcome it?
- Think back to a past data science project you worked on. If the powers that be asked you to change one of your data sources, and thus use different predictors, how would you alter your solution?
- Research has stated that 2.3 billion people have been affected by floods in the last two decades. Describe how you’d approach a data science project to predict upcoming floods in the next 100–500 years. These predictions can be used to build dams at correct locations to minimize loss.
livedoor
Peter Suderman
The promise of the internet, and social media in particular, was that it would not only allow anyone the opportunity to speak, but would also make it possible for anyone to precisely tailor what he reads, sees and hears online. News and information would no longer be mediated by newspaper editors, television producers and other gatekeepers. Instead, social media would allow direct access to individual voices in a feed custom-built by the user. It was a new frontier for both unregulated free expression and individual control.
In practice, the actual experience of social media, for many users, is not one of control but of virtual bombardment, in which a flood of ideas and opinions that are irritating, dull and often outright offensive often seem impossible to avoid. Yes, you can block, mute, unfollow, log off and even delete your account. But the prevalence of social media — the way in which it has become the mortar of everyday life, filling in the cracks of our time — has a way of enforcing a sense that there is no way to truly escape from its reach. The world of social media increasingly feels as if it is simply the world.
That world is one in which speech is often perceived not as an individual right, but as a public act, in which words and ideas are not your own, but a contribution to the collective. Social media has, in effect, socialized speech.
Amazon Kindle ダイレクト・パブリッシング
- 原稿と表紙を準備します。利用できるツールとリソースを確認します。
- 本の内容などが KDP のコンテンツ ガイドラインと品質ガイドラインに準拠していることを確認します。
- Amazon アカウントを使用して KDP にサインインするか、アカウントを新規作成します。
- お使いのブラウザーが最新バージョンであることを確認します。
- 「本棚」にアクセスします。「新しい本を作成」セクションで、「+ Kindle 本」をクリックします。
- 次の各セクションに情報を入力します。
- Kindle 本の詳細: タイトル、内容紹介、キーワード、カテゴリーなどを入力します。
- Kindle 本のコンテンツ: 原稿と表紙をアップロードします。 電子書籍をプレビューします。
- Kindle 本の価格設定: 配布権のある出版地域を選択します。ロイヤリティ プランを選択し、希望小売価格を設定します。
- 情報を入力したら、「Kindle 本を出版」をクリックします。
海外SEO情報ブログ
- <meta name=”robots” content=”noindex”>
ウェブページをインデックスさせたくない、言い換えると検索結果に表示させたくないときに使う。ミラーページを準備するときに便利。 - <meta name=”robots” content=”nofollow”>
このタグを記述すると、ロボットはページ内にあるリンク先(aタグで指定された別ページ)へアクセスしない。リンク先ページをキャッシュさせたくないときやPageRankを渡したくないときに便利。 - <meta name=”robots” content=”noarchive”>
サーチエンジンがウェブページをデータベースに保存するのを拒否できる。キャッシュリンクをクリックしても、直近にキャッシュされたページを閲覧することはできない。つまり現在のウェブページしか見れない。
ライブドア
EPUB書き出し機能で書き出されたEPUBファイルをKindleで閲覧するには、Kindleフォーマットに変換する必要があります。
ここでは比較的簡単なKindleプレビューツールを使った方法をご説明します。
- Kindle ダイレクト・パブリッシングのヘルプサイトから、Kindle プレビューツールをダウンロードします。
- Kindle プレビューツールをインストール後起動し、EPUBファイルをドラッグ&ドロップします。
- 自動的に変換が始まり、EPUBファイルと同じ場所に「Compiled-(ファイル名)」という名前のフォルダが作成されます。
- フォルダの中に、拡張子が.mobiになったファイルがあります。これをKindleに転送すれば、閲覧することができます。
OnDeck
PCでEPUBファイルを開く方法
- Adobe Digital Editions
- Readium(Google Chromeを起動し、アクセスする)
- Microsoft Edge (browser)
Adobe
InDesign ドキュメントを EPUB に書き出して、EPUB リーダーで出力を表示できます。
リフロー可能な EPUB 形式でドキュメントを書き出すことを選択できます。リフロー可能な EPUB ドキュメントの場合、EPUB リーダーは表示デバイスに応じてコンテンツを最適化できます。
ドキュメントが eInk デバイスのユーザーを対象としている場合には、リフロー可能な形式が適しています。また、リーダーのフォントやサイズを変更するオプションを提供する場合にも、リフロー可能な形式が推奨されます。
固定レイアウト形式でドキュメントを書き出すことを選択できます。固定レイアウト形式では、ドキュメントにオーディオ、ビデオ、および Edge コンテンツを含めることができます。
ナビゲーションボタン、ページ遷移、アニメーション、ハイパーリンクなどのコントロールを含んだインタラクティブドキュメントを、固定レイアウト形式で書き出すこともできます。
固定レイアウト形式は、多数のグラフィック、オーディオ、ビデオコンテンツを含んでいるドキュメントに適しています。この形式は子供の本、料理本、教科書、および漫画本に適しています。
Parmy Olson
Called Peltarion, the Stockholm-based startup has raised $16 million to date from investors and counts BMW, NASA, Ocado and 13 other organizations as early subscribers, with 800 more in line to try it out.
Crnkovic-Friis, their CEO, says that many companies have tried using other, off-the-shelf machine-learning tools like Google’s TensorFlow, Amazon’s Sage Maker and Microsoft’s Azure Machine Learning to build their own image-recognition or natural-language processing systems.
But these tools are “super complex,” he says. “You have to be an AI expert to use them.”
Crnkovic-Friis designed Peltarion to do for AI what WordPress (and before that, Dreamweaver) did for people who wanted to build websites but didn’t know HTML.
It uses a graphical interface to build and train a bespoke neural network, a computer system that’s inspired by the structure of a human brain. Software developers and junior data scientists who aren’t AI experts should be able to use it, Crnkovic-Friis says.
国際教養大学
Public Relations Society of America (PRSA)
Public relations is a strategic communication process that builds mutually beneficial relationships between organizations and their publics.
Chartered Institute of Public Relations (CIPR)
Public Relations is about reputation – the result of what you do, what you say and what others say about you.
Public Relations is the discipline which looks after reputation, with the aim of earning understanding and support and influencing opinion and behaviour. It is the planned and sustained effort to establish and maintain goodwill and mutual understanding between an organisation and its publics.
Shaun Nichols
Though Cambridge Analytica said it is pulling the plug in the US and UK, there is already some indication that the outfit – which has a non-trivial organizational structure – is more or less just going to rebrand under a different banner.
The UK’s official registrar of businesses and organizations, Companies House, lists an active company called Emerdata Limited, headquartered at the same offices as SCL Elections and run by much of the same management and investors as Cambridge Analytica. It even describes itself as a “data processing, hosting and related activities” organization.
For instance, Dr Alexander Taylor was appointed a director of Emerdata on March 28. That’s Cambridge Analytica’s acting CEO and data wizard Dr Alexander Taylor. Julian Wheatland is an Emerdata director who is also a director within the SCL network of organizations.
Jennifer and Rebekah Mercer are directors of Emerdata, and are the daughters of ultra-wealthy businessman Robert Mercer who created and bankrolled Cambridge Analytica. Billionaire Bob has given tens of millions of dollars to rightwing political efforts. Jennifer and Rebekah also had a hand in Cambridge Anal.
Her Story
Galignani
QuantCube
Le Monde
Décodex : nos outils contre les fausses informations
Utilisez les outils développés par Les Décodeurs pour vous aider à éviter les fausses informations :
- Fiables ou pas ? Testez les sites que vous consultez sur notre moteur de recherche (cliquez ici pour y accéder) ;
- Pour savoir en un coup d’œil si vous êtes sur un site fiable ou pas, installez notre extension pour les navigateurs Chrome (à télécharger ici) et Firefox (à télécharger ici) ;
- Vous voulez apprendre à vérifier l’information en ligne ? Lisez nos conseils pour éviter les fausses informations ;
- Besoin d’aide pour vérifier une info ? Interrogez notre robot Facebook (cliquez ici pour y accéder).
荻上チキ
特定のメディアの偏りばかりが目につくとしたら、それは観察する者が何かの立場に強くコミットメントしているためだ――
人と人とのコミュニケーションに、偏りが存在しない状態はない。この世に「真実そのもの」が仮にあったとしても、それをまっさらに伝えることのできる「なかだち」は存在しない。文字であろうが映像であろうが音であろうが、伝えられる情報量は有限だ。
ニュースは出来事を要約して伝えなければならないし、仮に無限の伝達が技術的に可能であろうと、人の時間は有限である。すべての情報は断片的で、切り取られたものだ。何かの断片的で編集された情報を手にしたうえで、「真実を知った」と思い込むのは誤っている。
週刊ポスト
〈世の中には3種類の嘘がある。『普通の嘘』、『大嘘』、そして『統計』だ〉──19世紀イギリスで首相を務めたベンジャミン・ディズレーリの言葉だ。根拠に乏しい理論ほど、統計が頻繁に用いられることを見抜いた至言であるが、この国にも“統計の皮を被った嘘”はあちこちにある。
例えば、法務省の出入国管理統計では、2016年の20代の海外渡航者は282万人で、ピーク時(1996年)の463万人から4割減っている。それをもって観光庁は、「若者の海外旅行離れを食い止める」と有識者検討会を設置している。
厚労省の人口動態調査では、1996年の20代人口は1953万人で、2016年は1238万人。この数字で“20代海外旅行率”を出すと、1996年は23.7%で、2016年は22.8%となり、実はほとんど変化がない。
また近年、〈少年事件「増えた」78%〉(朝日新聞2015年9月20日付)、〈少年非行「増えた」78%、内閣府調査、スマホの影響懸念〉(日経新聞2015年9月20日付)など、「少年犯罪の増加」を実感させる報道が多いが、それも怪しい。
記事になった内閣府の「少年非行に関する世論調査」は統計というより感想を集めたものだ。「少年による重大な事件が増えているという印象を持つ人」が78.6%いるというだけで、実際の犯罪増加を示しているわけではない。
警察庁統計によれば、刑法犯として検挙された少年(14~19歳)の数は、1980年代前半をピークに減少傾向で、最新の2016年統計では戦後最少を記録している。
David Z. Hambrick, Madeline Marquardt
Fake news can distort people’s beliefs even after being debunked. For example, repeated over and over, a story such as the one about the Pope endorsing Trump can create a glow around a political candidate that persists long after the story is exposed as fake. A study recently published in the journal Intelligence suggests that some people may have an especially difficult time rejecting misinformation. Asked to rate a fictitious person on a range of character traits, people who scored low on a test of cognitive ability continued to be influenced by damaging information about the person even after they were explicitly told the information was false. The study is significant because it identifies what may be a major risk factor for vulnerability to fake news.
David Rapp
Even when we know better, our brains often rely on inaccurate or misleading information to make future decisions. But why are we so easily influenced by false statements such as “vaccinations cause autism” or “30 million illegal immigrants live in the U.S.?”
People quickly download the inaccurate statements into memory because it’s easier than critically evaluating and analyzing what they’ve heard.
Later, the brain pulls up the incorrect information first because it’s less work to retrieve recently presented material. If it’s available, people tend to think they can rely on it. But just because you can remember what someone said, doesn’t make it true.
It’s even harder to avoid relying on misinformation when accurate and inaccurate information is mixed together.
We’re bombarded with tons of information all day; it’s a nightmare to critically evaluate all of it.
We often assume sources are reliable. It’s not that people are lazy, though that could certainly contribute to the problem. It’s the computational task of evaluating everything that is arduous and difficult, as we attempt to preserve resources for when we really need them.
Dan Coats
We expect Russia to continue using propaganda, social media, false-flag personas, sympathetic spokespeople and other means of influence to try to exacerbate social and political fissures in the United States.
There should be no doubt that Russia perceives its past efforts as successful and views the 2018 U.S. midterm elections as a potential target for Russian influence operations.
Throughout the entire community, we have not seen any evidence of any significant change from last year.
The Russians have a strategy that goes well beyond what is happening in the United States. While they have historically tried to do these types of things, clearly in 2016 they upped their game. They took advantage, a sophisticated advantage of social media. They are doing that not only in the United States but doing it throughout Europe and perhaps elsewhere.
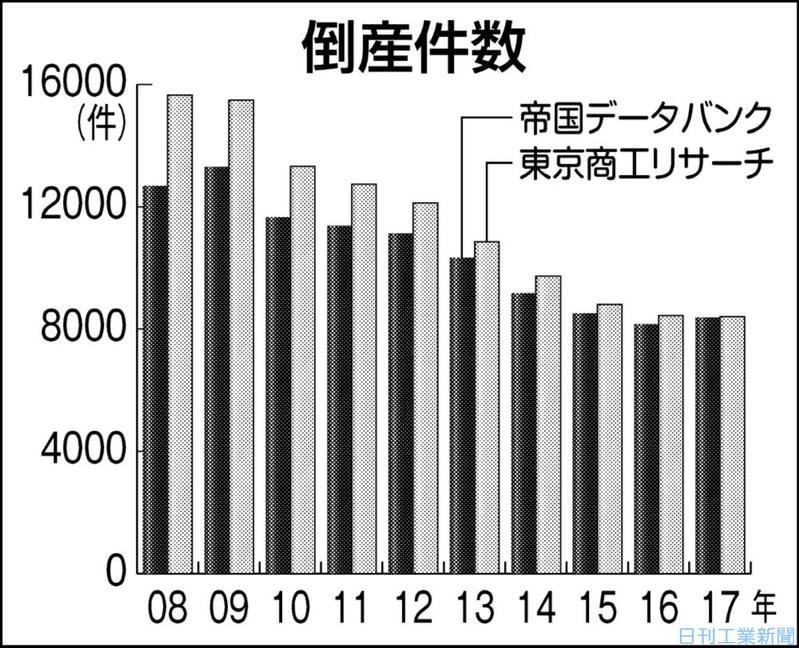
明豊
Niall Ferguson
You either love Donald Trump or you loathe him. You either adore Brexit or abhor it. This polarization has been fostered by the giant online social networks of our time.
Facebook encourages you to like or not like what you see in your Newsfeed. Twitter allows you to retweet or like other people’s tweets or block those users who offend your sensibilities.
In this binary world, there is not much room for ambivalence. I have had a tough time this year explaining even to friends why I can like some aspects of the Trump administration while at the same time disliking others.
Mark Zuckerberg
Franz Vollenweider
A fundamental feature of information processing dysfunction in psychosis is the inability of these patients to screen out, inhibit, filter or gate extranous stimuli and to attent selectively to salient features of the environment. Gating deficients may cause these subjects to become overloaded with excessive extroceptive and introceptive stimuli, which in turn could lead to a breakdown in cognitive integrity and difficulty in distinguishing self from nonself.
Stevan Dojcinovic
My country, Serbia, has become an unwilling laboratory for Facebook’s experiments on user behavior — and the independent, nonprofit investigative journalism organization where I am the editor in chief is one of the unfortunate lab rats.
Last month, I noticed that our stories had stopped appearing on Facebook as usual. I was stunned. Our largest single source of traffic, accounting for more than half of our monthly page views, had been crippled.
Surely, I thought, it was a glitch. It wasn’t.
Facebook had made a small but devastating change. Posts made by “pages” — including those of organizations like mine — had been removed from the regular News Feed, the default screen users see when they log on to the social media site. They were now segregated into a separate section called Explore Feed that users have to select before they can see our stories.
Adam Mosseri
There have been a number of reports about a test we’re running in Sri Lanka, Bolivia, Slovakia, Serbia, Guatemala, and Cambodia. Some have interpreted this test as a future product we plan to deliver globally. We currently have no plans to roll this test out further.
We always listen to our community about ways we might improve News Feed. People tell us they want an easier way to see posts from friends and family. We are testing having one dedicated space for people to keep up with their friends and family, and another separate space, called Explore, with posts from pages.
The goal of this test is to understand if people prefer to have separate places for personal and public content.
Ajit Pai
Roughly one-quarter of American newspapers have gone out of business since 1975, and many of those that remain are struggling. Today, only 18 percent of Americans read print newspapers regularly. Less than 10 percent under the age of 50 do. By a large margin, people instead turn to the internet for news.
カタヨリ荘
International Consortium of Investigative Journalists (ICIJ)
唐沢俊一
ツイッターでのつぶやき 「空が綺麗な季節になりました。去年、夫と子供と旅行した信州の空の青さを思い出すなあ。三人で食べたおそばもおいしかった。今年も行きたいな」
繊細チンピラA 「はいはい、夫と子供いるぞ自慢ですか、いい気なものですね。独身女を見下すのがそんなに楽しいですか」
繊細チンピラB 「私の亭主は毎晩残業で、この何年か、旅行なんかしたことないですよ。毎年旅行とは結構なご身分だこと。旅行にも行けない人間たちがこのつぶやき読んでどういう気分になるか、考えたこともないんでしょうね」
繊細チンピラC 「私の子供はそばアレルギーで、おそば屋さんの近くにも立ち寄れません。そばで死ぬほど苦しむ子がいるんですよ。そういう子を持った親の気持ちをおもんぱかる気持ちがあったら、こんな文章は書けないと思います」
繊細チンピラD 「私の家はうどん屋です。秋になったらおそばを食べないといけないんですか? うどん屋はつぶれてもかまわないって言うんですね? なんて自分勝手な!」
山田ズーニー
話をしていて、なぜかつまらないと私が感じる人の共通点は、1つはっきりある。
「予定調和」だ。
もちろん会話は二人で分担するものだから、相手に予定調和な会話をさせている責任の半分はわたしにある。それを認めたうえで、
そういう予定調和の人は、返答のスピードがはやい。すぐ、はずれていない言葉を返してくださる。ためにもなる。
日ごろよく勉強をされていることが感じられるし、頭の回転もはやそう。ふいの沈黙もなく、よどみなく、ポンポン、安心して会話がつづけられる。
でも、それは、「心がやすまる」というのとは、どこかちがう。
人が、からだの、どれくらいの深さから言葉を発しているか?
というと、この予定調和な感じがする人は、胸の上のあたりに、「返答用のファイルボックス」がある感じだ。
The New York Times Editorial Board
 At 2:35 p.m. on Monday, the fearless Maltese journalist Daphne Caruana Galizia published a characteristically blunt post on her influential blog accusing leading politicians of corruption.
At 2:35 p.m. on Monday, the fearless Maltese journalist Daphne Caruana Galizia published a characteristically blunt post on her influential blog accusing leading politicians of corruption.
“There are crooks everywhere you look now,” she concluded. “The situation is desperate.”
Less than 30 minutes later, the car she was driving was blown to pieces.
For journalists around the world, this is the new normal.
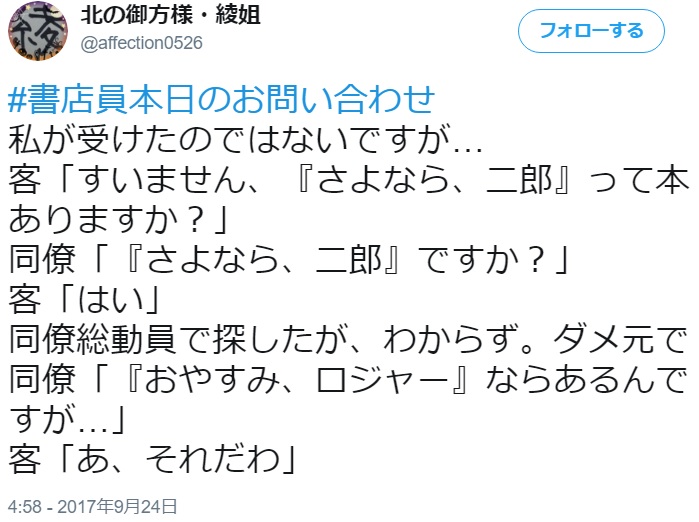
北の御方様・綾姐
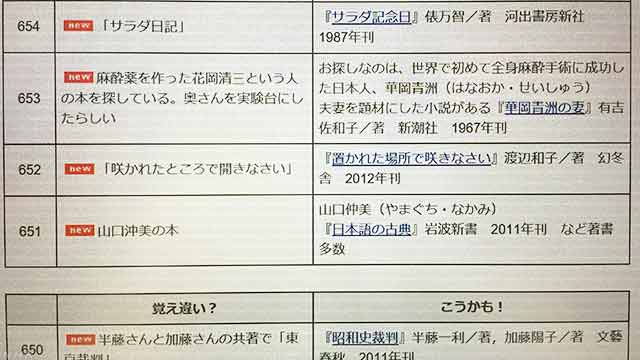
福井県立図書館
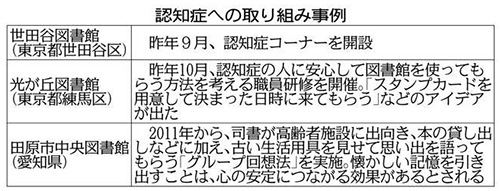
赤田康和, 塩原賢
書店が地域に1店舗もない「書店ゼロ自治体」が増えている。出版取り次ぎ大手によると、香川を除く全国46都道府県で420の自治体・行政区にのぼり、全国の自治体・行政区(1896)の2割強を占める。「文化拠点の衰退」と危惧する声も強い。
全国の書店数は1万2526店で、2000年の2万1654店から4割強も減った(書店調査会社アルメディア調べ、5月現在)。人口減や活字離れがあるほか、書店の売り上げの6~7割を占める雑誌の市場規模は10年前の6割に縮小。紙の本の市場の1割を握るアマゾンなど、ネット書店にも押される。経営者の高齢化やコンビニの雑誌販売なども影響する。
明報新聞網
Le Monde
Après l’annonce en janvier d’un plan dit de « nettoyage » pour « reconquérir la souveraineté chinoise sur Internet », le gouvernement chinois a demandé, le 11 juillet, aux entreprises de télécommunications de fermer tout accès aux VPN avant le 1er février 2018. Déjà, samedi 29 juillet, Apple a, sur demande des autorités chinoise, retiré de son magasin d’applications en ligne tous les VPN qui s’y trouvaient.
En Russie également les lois de contrôle du Web se sont multipliées ces dernières années. Vladimir Poutine a signé, le week-end du 29 au 30 juillet, un projet de loi adopté par le Parlement interdisant de facto les VPN dans le pays, ainsi que d’autres logiciels permettant de contourner la censure, comme le navigateur Tor. Une décision justifiée par le Kremlin comme nécessaire à la lutte contre le terrorisme, le trafic de drogue et d’autres délits.
Adam Segal
Reports this month that the United Arab Emirates orchestrated the hacking of a Qatari news agency, helping to incite a crisis in the Middle East, are as unsurprising as they are unwelcome. For years, countries — in particular Russia — have used cyberattacks and the dissemination of disinformation through social media and news outlets to provoke protests, sway elections and undermine trust in institutions. It was only a matter of time before smaller states tried their hand at these tactics.
With few accepted rules of behavior in cyberspace, countries as big as China or as small as Bahrain can be expected to use these kinds of attacks. And they may eventually spill over into real-world military conflicts.
Andrey Krutskikh
When humanity realized the horror of biological weapons, it banned them. We are in the same situation right now. We should avoid the mistakes of the Atomic Age, when we first armed ourselves sufficiently to destroy each other, and then began to disarm.
In our wisdom, we should agree not to militarize cyberspace, and set some international ground rules.
We have one small task ahead – convincing the United States and NATO members. But they need to understand that we are all in the same boat, and must row in the same direction.
The main platforms for promoting the new norms should be the UN and the OSCE.
福嶋聡
三田氏は、図書館が著作者の権利を制限することによって成り立っていることを指摘、作家の窮状を訴え、諸外国の例にならって「公共貸与権」の重視のもと、具体的な作家への保障を求める。図書館側の人たちは、争点となっている「複本」(予約者数の多いベストセラーを何冊も買い込むこと)も指摘されるほど多いわけではなく、自分たちは限られた、しかも削減されつつある予算の中で必死に頑張っている、と主張する。
どちらの言い分も、もっともである。双方とももっともだから、最後には「お互いいがみあっている場合ではない。作家も図書館も連帯して、国から予算をぶんどろう。」、表現が荒っぽすぎるかもしれないが、つまるところこういう結論になる。
ところが、現実には国も自治体も台所事情は火の車である。経済状況も相変らず悪い。だとすれば、先の結論は余り生産性を期待できるものではない。
明らかに読者の視点が欠落している。あるいは、利用者の視点が。
読者や利用者のことを忘却しているわけではない。欠落しているのはその視点なのである。
北方ジャーナル
Martin Untersinger
La question de savoir si Lazarus est effectivement piloté par Pyongyang est encore plus ardue. Le FBI, après une enquête sur le réseau de Sony Pictures avait conclu à la responsabilité de la Corée du Nord. Mais les preuves avancées étaient très minces. Non seulement l’attribution d’attaques informatiques à un Etat est techniquement très difficile, mais elle repose souvent fréquemment sur des éléments collectés par des agences de renseignement, par définition difficilement publiables sans mettre en péril leur source, qu’elle soit technique ou humaine.
« Le besoin de protéger des sources et des méthodes sensibles nous empêche de partager toutes les informations », écrivait d’ailleurs le FBI en novembre 2016.
Freedom of the Press Foundation
 SecureDrop
SecureDrop
Our open-source whistleblower submission system
 Secure the News
Secure the News
Tracking and promoting the adoption of HTTPS by news organizations.
 FOIA Lawsuits
FOIA Lawsuits
Suing the government for transparency.
 Digital Security Training
Digital Security Training
Teaching others to use digital security tools, one newsroom at a time.
Edward Snowden
Julian Assange
 The UK has said it will arrest me regardless. Now the US CIA director [Mike] Pompeo and the US attorney general [Jeff Sessions] have said that I and other WikiLeaks staff have no rights and that my arrest and the arrest of other staff is a priority. That is not acceptable … Our publications are proceeding at speed and that speed in relation to [recent high profile leaks about the CIA] is accelerating.
The UK has said it will arrest me regardless. Now the US CIA director [Mike] Pompeo and the US attorney general [Jeff Sessions] have said that I and other WikiLeaks staff have no rights and that my arrest and the arrest of other staff is a priority. That is not acceptable … Our publications are proceeding at speed and that speed in relation to [recent high profile leaks about the CIA] is accelerating.
山岡淳一郎
大震災は、社会の底に沈んで見えなかった矛盾を浮かび上がらせる。「空気」のように感じていた制度を具体的に生活の場面に押し出してくる。私たちが暮らす、この国の実相は危急存亡の危機によって「可視化」される、といってもいいだろう。
東日本大震災で、露わになった権力機構の弱点のひとつが「情報共有力の無さ」だ。大規模な原発災害を引き起こした以上、大本営発表式の発信ではなく、正確で質の高い情報を、いかに被災者、周辺地域、非被災地の国民、さらに国際社会と「共有」するかが問われる。「5W1H」で、いま福島原発で何が起きていて、それに誰がどう対応しているのか、悪い方向へ転じたら、どんな危険があるのかといったメッセージを国際機関と連携して公表することが求められる。上意下達の発信ではなく、「共有」が重要になってくる。
ところが、文部科学省の「緊急時迅速放射能影響予測ネットワークシステム(SPEEDI)」のデータが公表されたのは震災発生から2週間近く経過してからだった。
石原真樹
Katie Benner, Sui-Lee Wee
Apple, complying with what it said was a request from Chinese authorities, removed news apps created by The New York Times from its app store in China.
The move limits access to one of the few remaining channels for readers in mainland China to read The Times without resorting to special software. The government began blocking The Times’s websites in 2012, after a series of articles on the wealth amassed by the family of Wen Jiabao, who was then prime minister, but it had struggled in recent months to prevent readers from using the Chinese-language app.
Apple removed both the English-language and Chinese-language apps from the app store in China. Apps from other international publications, including The Financial Times and The Wall Street Journal, were still available in the app store.
山本達也
ソーシャルメディアは、エジプトの人々に「我々は一人ではないのだ」、「同じフラストレーションを溜めている人々は他にもいるのだ」、「同じ夢を共有している人々がいるのだ」、「多くの人が自由を気にかけているのだ」ということを気づかせた。こうしたソーシャルメディアを介した「心理的な連帯」と「想いの同期化」が、これまでのエジプト社会で人々を行動に転嫁させることなく思いとどまらせていた「恐怖の心理的な壁」(fear of barrier psychological)を乗り越えさせたという。
つまり、エジプトの若者層を突き動かしたのは、ある種の「単純な正義感」であり、そこには政治的なイデオロギーも党派性も見当たらない。しかし、それゆえに、若者たちの主張は他の若者たちに簡単に伝播し、共感が共感を呼ぶことで、爆発的な勢いを獲得することができたのである。
カギは「心理的な連帯」と「想いの同期化」であるが、それを可能とするのは「共感」を呼ぶことのできるコンテンツやメッセージの有無である。
池田信夫, 伊藤春香
私がNHKに勤務していたころ教わったのは、「典型的な視聴者は、50歳の専業主婦で高卒だと思え」ということだった。(池田)
電通の先輩が、「CMは偏差値40の人にも理解できるものじゃなきゃダメ。この会社にいる時点で普通ではないと自覚しろ。世間にはおそるべき量のおそるべきバカがいる。そしてそれが日本の『普通の人』だ」って言ってたの、一番役に立ってる教えの一つだ。(伊藤)
Michael J. I. Brown
This month there’s been a hoopla about a mini ice age, and unfortunately it tells us more about failures of science communication than the climate. Such failures can maintain the illusion of doubt and uncertainty, even when there’s a scientific consensus that the world is warming.
The story starts benignly with a peer-reviewed paper and a presentation in early July by Professor Valentina Zharkova, from Northumbria University, at Britain’s National Astronomy Meeting.
The paper presents a model for the sun’s magnetic field and sunspots, which predicts a 60% fall in sunspot numbers when extrapolated to the 2030s. Crucially, the paper makes no mention of climate.
The first failure of science communication is present in the Royal Astronomical Society press release from July 9. It says that “solar activity will fall by 60 per cent during the 2030s” without clarifying that this “solar activity” refers to a fall in the number of sunspots, not a dramatic fall in the life-sustaining light emitted by the sun.
The press release also omits crucial details. It does say that the drop in sunspots may resemble the Maunder minimum, a 17th century lull in solar activity, and includes a link to the Wikipedia article on the subject. The press release also notes that the Maunder minimum coincided with a mini ice age.
But that mini ice age began before the Maunder minimum and may have had multiple causes, including volcanism.
Crucially, the press release doesn’t say what the implications of a future Maunder minimum are for climate.
成毛眞
 「捨て方」とは、バカ情報には触れるなとか、情報は整理しなくていいとか、ネットニュースをチェックしまくるのは愚の骨頂とか、メモをきれいにとる必要はないので、捨てることを前提とした紙にとればいいとか——とにかく、「触れる情報を絞り込み、必要最低限のもの以外は溜めることを考えない」というものです。
「捨て方」とは、バカ情報には触れるなとか、情報は整理しなくていいとか、ネットニュースをチェックしまくるのは愚の骨頂とか、メモをきれいにとる必要はないので、捨てることを前提とした紙にとればいいとか——とにかく、「触れる情報を絞り込み、必要最低限のもの以外は溜めることを考えない」というものです。
食べ物同様、情報も、おびただしい数のものが、品質を問わず世に溢れています。全部を摂取し、消化することはどんな人間にも不可能です。アウトプットしない情報をすべて入手している暇も胃の容量もありません。
だからといって、情報をすべて拒めばいいというものでもない。それでは社会的に死んでしまいます。
『情報の「捨て方」』は、情報過多な現代社会を生き抜くため、情報に溺れないようにし、そして、情報という栄養が不足しないようにする方法を記しています。
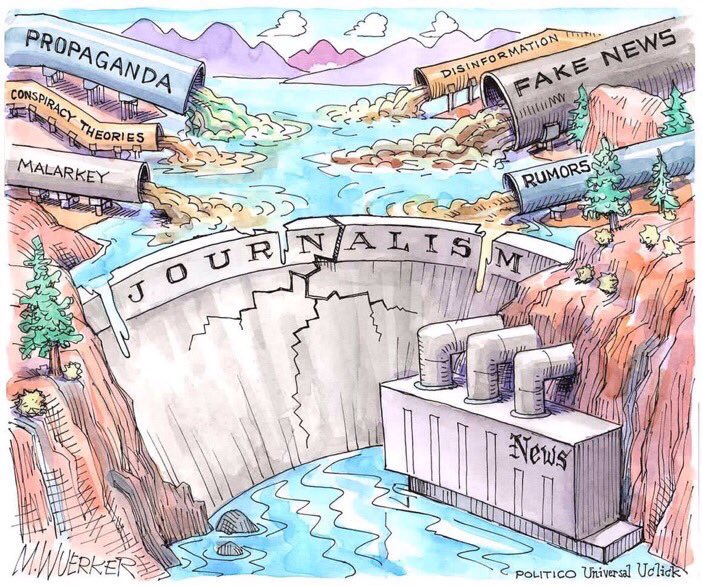
Matt Wuerker
藤田徳人
子供を教育するときに、親は「偉いね」「すごいね」と言ってほめて <やる気> を出させて成績を上げさせようとするものです。実際子供のやることなど、偉くもすごくもないのです。ですが、そうやって子供を騙すことによって意欲を芽生えさせながら教育します。
受験もそうです。神社にお参りして、おみくじで大吉を引いて「試験は必ず合格する」なんて書いてあれば、それだけで合格した気分になり、次の日から勉強意欲がわくというもの。もし、そういう暗示も何もなく、「そんな簡単に合格するわけがない」という現実ばかりを突きつけられていたのでは、実際勉強する気力を生み出すことは難しいでしょう。
映画やドラマの世界もそうです。役者さんたちは、あくまで芝居をしているわけであって、嘘の笑い、嘘の涙を作って物語をすすめています。「これは芝居だ」とわかっていても、人はそれを見て自分が主人公になった気分になり、普段得られない喜怒哀楽の感情やドキドキ感を得ようとします。そういったものを見ている人はむしろ、無意識的に「騙されよう」としています。そして騙されれば騙されるほど、その感動は深くリアルなものとして自分自身にフィードバックされるわけです。
多くの男性はアダルトビデオを見て興奮しますが、これだって「自分はこの女優とエッチしている」という妄想を刺激しているだけにすぎません。ですが、男性たちは必死になってそのバーチャルな世界にわざと入りこもうとし、そして強い性的興奮を得ようとするのです。これらは全て、自ら騙されようとしているから成り立つもので、人はいかに騙されたがっているかということがわかります。騙されるほどに快感を得ることができるからです。
Randall Beard
The formats where action exceeds trust by the greatest margin share a common attribute: Easy access to products/services. You like it, you buy it. Online and mobile formats make it exceptionally easy for consumers to live in the moment and take quick action on the advertisement. Often, consumers simply click a link and they’re directed to a place where they can receive more information or purchase the item.
Sheri Rose
Institute for Propaganda Analysis
Glittering Generalities:
Glittering generalities was one of the seven main propaganda techniques identified by the Institute for Propaganda Analysis in 1938. It also occurs very often in politics and political propaganda. Glittering generalities are words that have different positive meaning for individual subjects, but are linked to highly valued concepts. When these words are used, they demand approval without thinking, simply because such an important concept is involved. For example, when a person is asked to do something in “defense of democracy” they are more likely to agree. The concept of democracy has a positive connotation to them because it is linked to a concept that they value. Words often used as glittering generalities are honor, glory, love of country, and especially in the United States, freedom. When coming across with glittering generalities, we should especially consider the merits of the idea itself when separated from specific words.
モーリー・ロバートソン
放射能、TPP、子宮頸がんワクチン、大麻など、ひとたび「○○が怖い」「○○は穢(けが)れている」という流れになったとき、日本では多くの人々が目の前にある重い課題をゼロベースで考え抜くことを放棄し、「信じたいことを信じる」傾向が強くなる。みんな同じことを考えるはずだ、そうでないヤツはけしからん…。
この脆弱な言論空間に、スマートで巧妙な情報操作を行なう集団が現れたらどうなるか? たとえ「極右政権誕生」という形はとらなくとも、様々な形で“排外的な空気”が社会全体に染み渡っていく可能性は極めて高いでしょう。
マスメディアが没落してあらゆる情報が水平化した現在、情報の信頼性や真贋、そして「奥行き」は受け手側が判断しなければいけなくなりました。具体的な見分け方はケースバイケースですが、ひとつだけ言えることがあります。
自分や自分の属する集団を無批判に持ち上げる(「今のままが一番」「日本人で良かった」など)ばかりの報道や政治運動は、よく考えてみれば、別の誰かにとっては極めて排他的なものです。そんな言説が力を持つ世の中では、いつしかその排他性が自分にも向かってくる。これからの時代、そのことは誰もが肝に銘じておく必要があるでしょう。
Frostbeard Studio
News.com.au
デジタル大辞泉
大本営発表
- 太平洋戦争中、大本営が国民に向けて発表した、戦況に関する情報。末期には、戦況が悪化しているのにもかかわらず、優勢であるかのような虚偽の発表をくり返した。
- 転じて、政府や有力者などが発表する、自分に都合がよいばかりで信用できない情報。
Sarah Harrison
 Despite the mounting legal and political pressure coming from Washington, we continue to publish valuable material, and submissions keep pouring in. There is a desperate need for our work: The world is connected by largely unaccountable networks of power that span industries and countries, political parties, corporations and institutions; WikiLeaks shines a light on these by revealing not just individual incidents, but information about entire structures of power.
Despite the mounting legal and political pressure coming from Washington, we continue to publish valuable material, and submissions keep pouring in. There is a desperate need for our work: The world is connected by largely unaccountable networks of power that span industries and countries, political parties, corporations and institutions; WikiLeaks shines a light on these by revealing not just individual incidents, but information about entire structures of power.
While a single document might give a picture of a particular event, the best way to shed light on a whole system is to fully uncover the mechanisms around it — the hierarchy, ideology, habits and economic forces that sustain it. It is the trends and details visible in the large archives we are committed to publishing that reveal the details that tell us about the nature of these structures. It is the constellations, not stars alone, that allow us to read the night sky.
共同通信
Robert Hunziker
Fukushima is a national/worldwide emergency that is the worst kept secret ever because everybody knows it is happening; it is current; it is alive; it is deadly; it has killed and will kill many more as well as maim countless people over many decades.
Yet, the Abe administration is talking to Olympic officials about conducting Olympic events, like baseball, in Fukushima for Tokyo 2020. Are they nuts, going off the deep end, gone mad, out of control? After all, TEPCO readily admits (1) the Fukushima cleanup will take decades to complete, if ever completed, and (2) nobody knows the whereabouts of the worlds most deadly radioactive blobs of sizzling hot masses of death and destruction, begging the question: Why is there a Chernobyl Exclusion Zone of 1,000 square miles after one nuclear meltdown 30 years ago, but yet Fukushima, with three meltdowns, each more severe than Chernobyl, is already being repopulated? It doesn’t compute!
The short answer is the Abe administration claims the radioactivity is being cleaned up. A much longer answer eschews the Abe administration by explaining the near impossibility of cleaning up radioactivity throughout the countryside. There are, after all, independent organizations with boots on the ground in Fukushima that tell the truth, having measured dangerous levels of radiation throughout the region where clean up crews supposedly cleaned up.
The Columbia Journalism Review article, intentionally or not, paints a picture of “journalism by government decree” in Japan, which gainsays any kind of real journalism. It’s faux journalism, kinda like reading The Daily Disneyworld Journal & Times.
Martin Fackler
Abe and his supporters on the nationalistic right seized on missteps by the Asahi in its coverage of Fukushima and sensitive issues of World War II-era history to launch a withering barrage of criticism that the paper seemed unable to withstand. The taming of the Asahi set off a domino-like series of moves by major newspapers and television networks to remove outspoken commentators and newscasters.
Political interference in the media was one reason cited by Reporters Without Borders in lowering Japan from 11th in 2010 to 72nd out of 180 nations in this year’s annual ranking of global press freedoms, released on April 20, 2016.
日本新聞協会
Lawrence Lessig
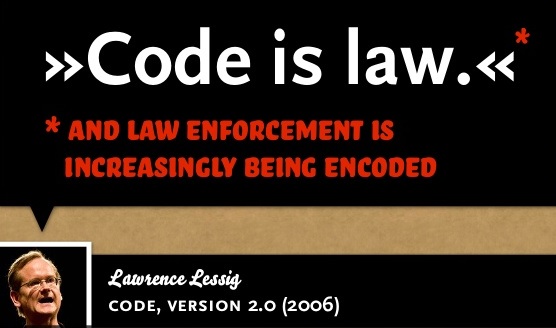 It is proper to let the market develop first. But as the Constitution checks and limits what Congress does, so too should constitutional values check and limit what a market does. We should test both the laws of Congress and the product of a market against these values. We should interrogate the architecture of cyberspace as we interrogate the code of Congress.
It is proper to let the market develop first. But as the Constitution checks and limits what Congress does, so too should constitutional values check and limit what a market does. We should test both the laws of Congress and the product of a market against these values. We should interrogate the architecture of cyberspace as we interrogate the code of Congress.
Unless we do, or unless we learn how, the relevance of our constitutional tradition will fade. The importance of our commitment to fundamental values, through a self-consciously enacted constitution, will fade. We will miss the threat that this age presents to the liberties and values that we have inherited. The law of cyberspace will be how cyberspace codes it, but we will have lost our role in setting that law.