ビッグデータと ブロックチェーンと AI が
今までのビジネスモデルを時代遅れにし
組織の中での人間の役割を変えていく
ビッグデータで
明確な戦略を立てたり
変化し続ける環境を
よりよく理解することができ
ブロックチェーンで
データソースが統合され
矛盾への対処や
エラーや誤報告の特定が
容易にできるようになり
AI で
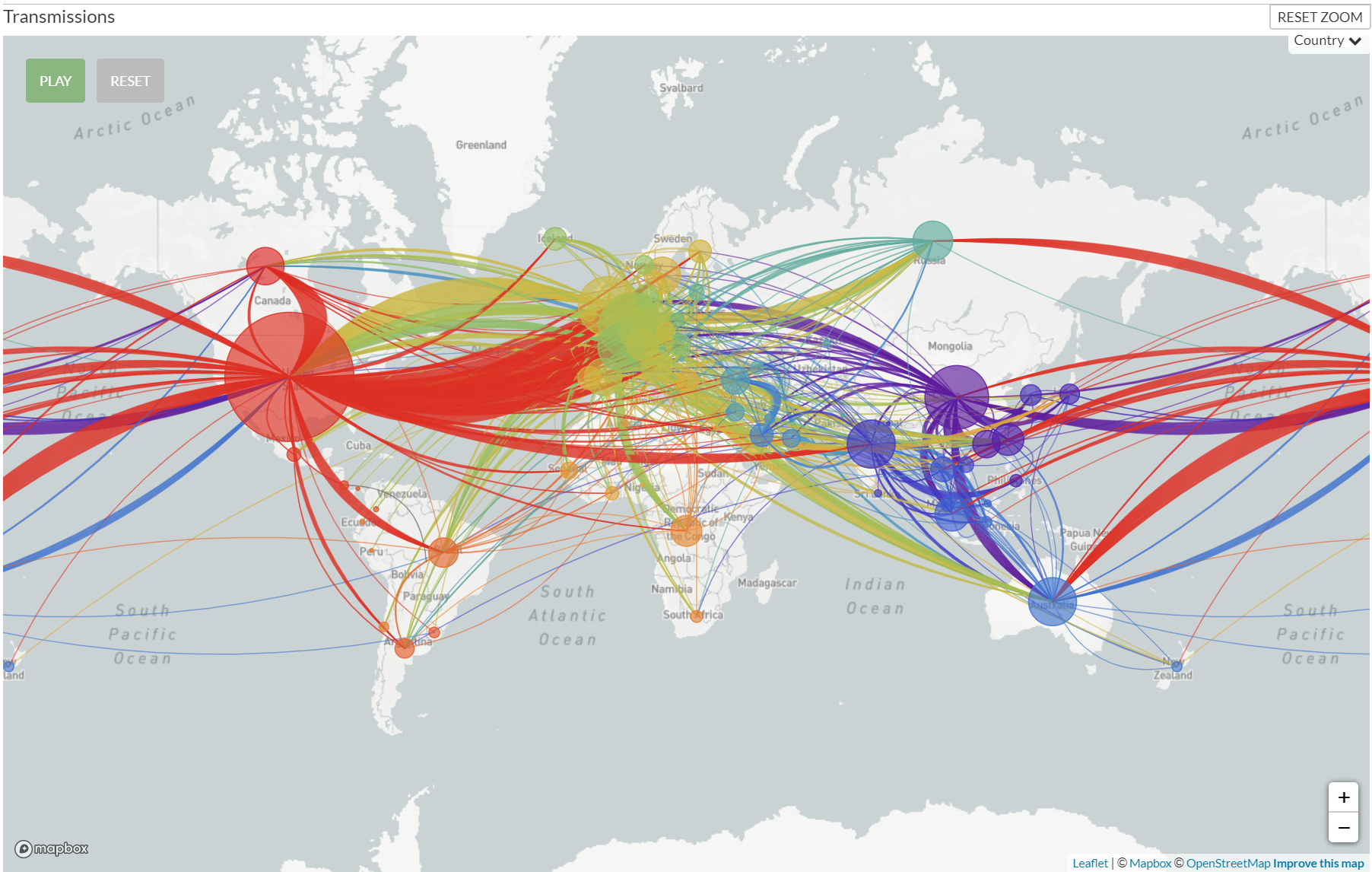
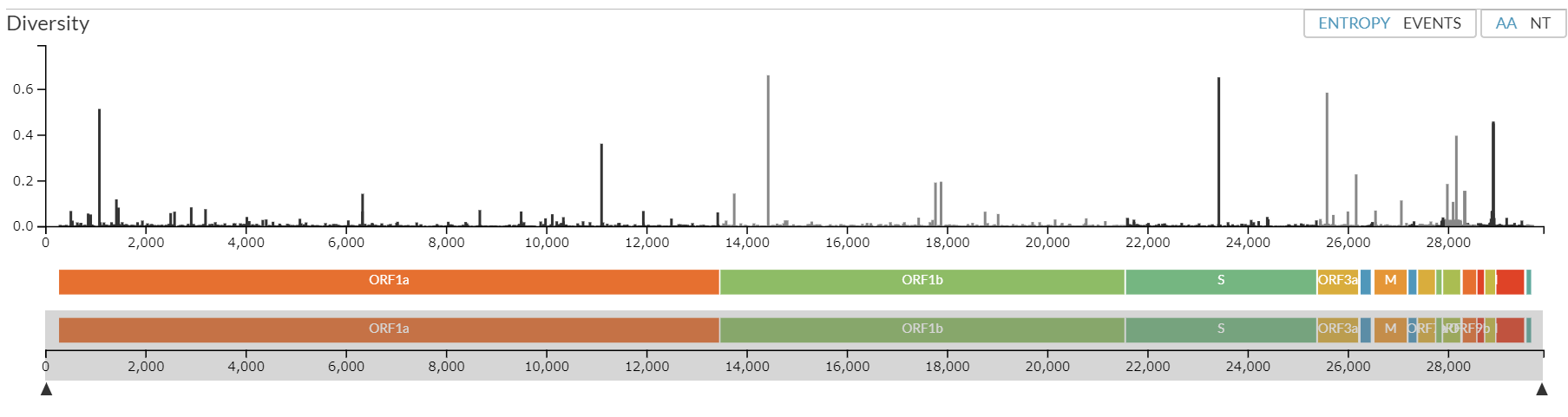
特定地域の状況の監視や予測が
現地に行かないでもできるようになる
ビッグデータ 人工衛星からのデータ ブロックチェーン AI などを
複合的にそして積極的に利用することで
開発の分野でも人道援助の分野でも
大きな貢献を続けることができる
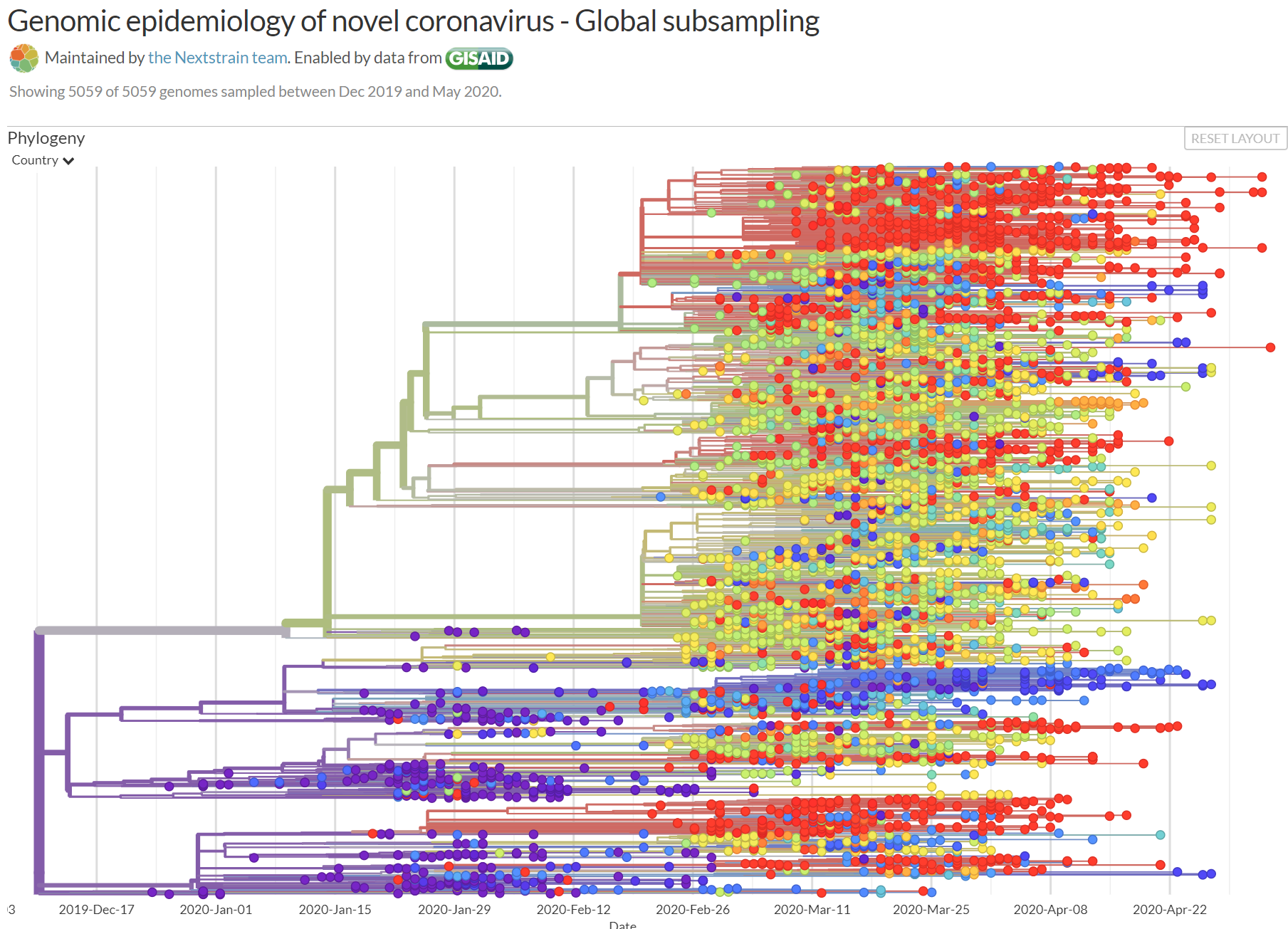
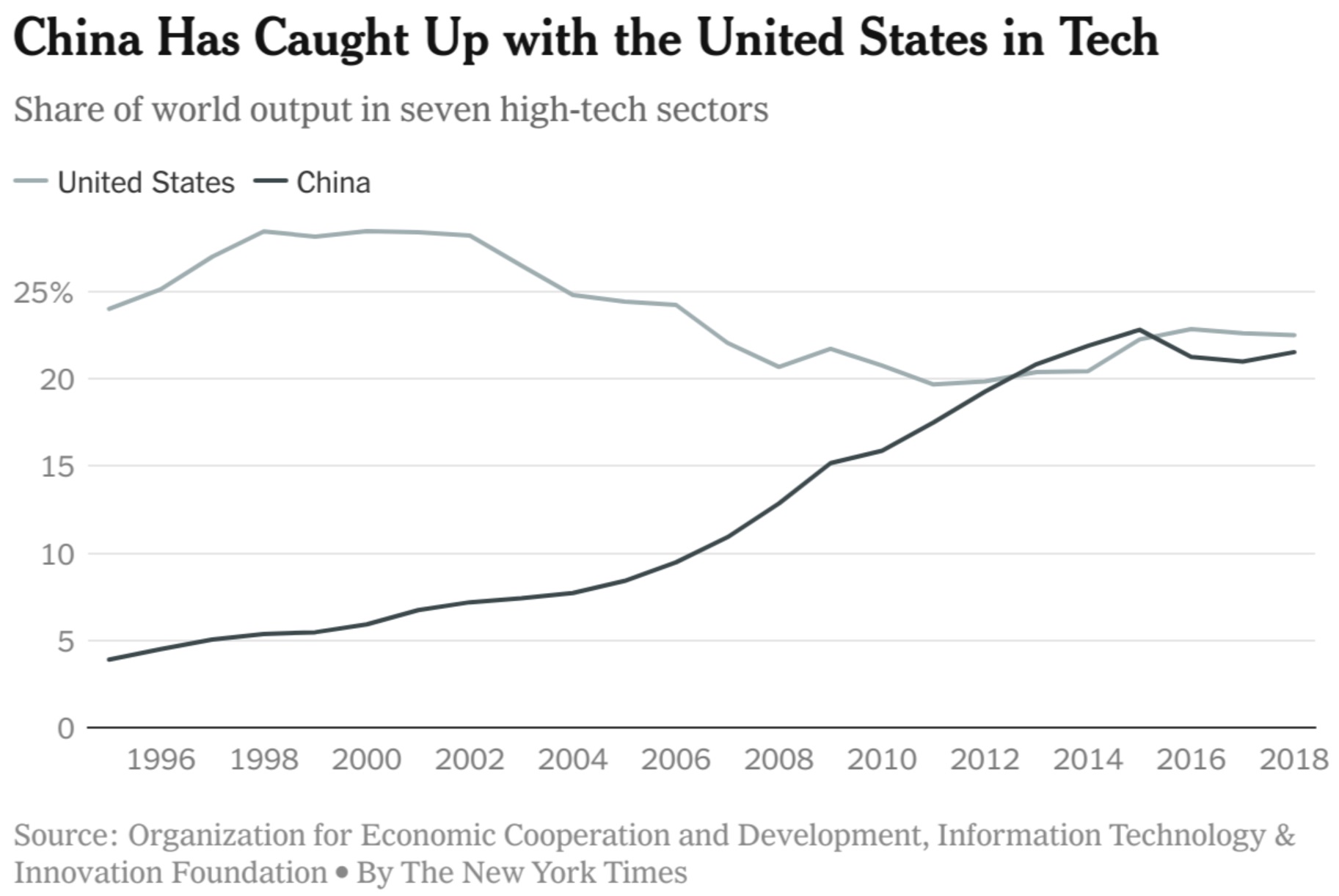
COVID-19 の流行は
ビッグデータと ブロックチェーンと AI の利用の各国の実力の差を
世界中の人たちにまざまざと見せつけることになってしまった
二つの大国の優位性が明らかになり
二つの大国のやり方の違いも明らかになった
テクノロジーの応用の仕方や運用の仕方が違うのはもちろん
その裏にある価値観の違いがお互いの不信感を増幅している
人権とかプライバシーといった価値に重きを置く大国と
最大多数の最大幸福を追求する大国は
お互いの非難を繰り返している
ビッグデータと ブロックチェーンと AI の利用についての
不平等は広がるばかり
各国がますます内向きになるなかで
それぞれの国から不平等の解消についての議論は出てこない
ブロックチェーンのおかげで
ペーパーレスが進んだ国と
そういうことが考えられない国との
事務量の差は広がるばかり
オンライン決済が浸透し
キャッシュレスが浸透した国と
浸透していない国との
利便性の違い大きくなり
恩恵の差は広がるばかり
感染症の脅威があるかないかを
知ることのできるシステムのある社会と
それらしいシステムしかない社会との差は
驚くほど大きい
行方不明になった人が簡単に見つかる社会と
見つからない社会とでは
間違いなく何かが違う
ビッグデータと ブロックチェーンと AI の
利用についての不平等を解消していかなければ
現在の経済的な貧富の差は
現在とは違った形で
現在よりはるかに大きなものになってあらわれる
ビッグデータと ブロックチェーンと AI の
競争に参加している人の数は
びっくりするほど少ない








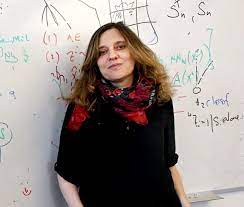 When MIT professor Regina Barzilay received her breast cancer diagnosis, she turned it into a science project. Learning that the disease could have been detected earlier if doctors had recognized the signs on previous mammograms, Barzilay, an expert in artificial intelligence, used a collection of 90,000 breast x-rays to create software for predicting a patient’s cancer risk.
When MIT professor Regina Barzilay received her breast cancer diagnosis, she turned it into a science project. Learning that the disease could have been detected earlier if doctors had recognized the signs on previous mammograms, Barzilay, an expert in artificial intelligence, used a collection of 90,000 breast x-rays to create software for predicting a patient’s cancer risk.

 The Internet of Things (IoT) is connecting people, places, and devices at a rapid pace. With the surge of connected devices comes the demand and necessity to implement security features for IoT devices. Qualcomm Technologies has a long heritage of providing mobile security solutions. Today, our security solutions are found in billions of commercial devices around the world, utilizing our proven mobile solutions for consumer and industrial IoT applications.
The Internet of Things (IoT) is connecting people, places, and devices at a rapid pace. With the surge of connected devices comes the demand and necessity to implement security features for IoT devices. Qualcomm Technologies has a long heritage of providing mobile security solutions. Today, our security solutions are found in billions of commercial devices around the world, utilizing our proven mobile solutions for consumer and industrial IoT applications. AIとロボット技術が結合したスマートマシンの興隆で、人間の倫理的判断能力が矮小化され、前近代的な部族政治がふたたび姿を現すのだろうか。それとも休息を必要とする人間労働が、超効率的なロボットに置き換えられることで大量失業が生じるのか。
AIとロボット技術が結合したスマートマシンの興隆で、人間の倫理的判断能力が矮小化され、前近代的な部族政治がふたたび姿を現すのだろうか。それとも休息を必要とする人間労働が、超効率的なロボットに置き換えられることで大量失業が生じるのか。